Investigation into the contracting practices of the Canada Border Services Agency related to the development of the ArriveCAN application
Special report to Parliament
March 12, 2026
For more information, contact:
Office of the Privacy Commissioner of Canada
30 Victoria Street
Gatineau, Quebec K1A 1H3
Toll-free: 1-800-282-1376
Phone: 819-994-5444
TTY: 819-994-6591
© His Majesty the King in Right of Canada, for the Office of the Privacy Commissioner of Canada 2026.
Cat. No.: IP54-120/2026E-PDF
ISBN: 978-0-660-98722-4
Letter to the Speaker of the Senate
BY EMAIL
March 12, 2026
The Honourable Raymonde Gagné, Senator
Speaker of the Senate
Senate of Canada
Ottawa, Ontario K1A 0A4
Dear Madam Speaker:
I have the honour to submit to Parliament the Special Report of the Office of the Privacy Commissioner of Canada entitled Investigation into the contracting practices of the Canada Border Services Agency related to the development of the ArriveCAN application. This tabling is done pursuant to sections 39(1) and 40(1) of the Privacy Act.
Sincerely,
(Original signed by)
Philippe Dufresne
Commissioner
Letter to the Speaker of the House of Commons
BY EMAIL
March 12, 2026
The Honourable Francis Scarpaleggia, M.P.
Speaker of the House of Commons
House of Commons
Ottawa, Ontario K1A 0A6
Dear Mr. Speaker:
I have the honour to submit to Parliament the Special Report of the Office of the Privacy Commissioner of Canada entitled Investigation into the contracting practices of the Canada Border Services Agency related to the development of the ArriveCAN application. This tabling is done pursuant to sections 39(1) and 40(1) of the Privacy Act.
Sincerely,
(Original signed by)
Philippe Dufresne
Commissioner
Table of contents
- Sub-issue 1: Did the ArriveCAN contracts and TAs contain appropriate clauses to ensure the protection of travellers’ personal information that contractors had access to
- Sub-issue 2: Did the CBSA comply with security requirements for ArriveCAN-related contracts and TAs
- Sub-issue 3: Did the CBSA implement adequate safeguards to protect personal information collected through ArriveCAN that was accessed by contractors
Procurement practices that may impact privacy
Annex A: ArriveCAN major releases
Annex B: Security levels for sensitive government information and assets
Introduction
The Office of the Privacy Commissioner of Canada (OPC) has concluded an investigation into the contracting practices of the Canada Border Services Agency (CBSA) related to the development of the ArriveCAN app, including the measures implemented by the CBSA to mitigate risks associated with the handling of travellers’ personal information by contractors.
The ArriveCAN app was designed to respond to the COVID-19 pandemic by digitizing the collection of traveller information and expediting the processing of travellers at the border. Given the urgent need for IT professional services, and due to limited internal capacity, the CBSA relied extensively on contractors for ArriveCAN program delivery, including the development and maintenance of the app.
While there are no provisions in the Privacy Act that prevent government institutions from using external contracted resources, outsourcing can raise additional privacy risks, particularly if contractors require access to government information or assets. It is therefore essential for institutions to consider the privacy implications carefully when contracting out their activities and take steps to ensure that appropriate safeguards are implemented to mitigate the risks associated with outsourcing and to protect personal information that contractors have access to.
This Special Report to Parliament underscores the strong nexus between contracting and privacy. Contracts serve as the legal framework to define how personal information will be handled and safeguarded, which is crucial for government outsourcing and to ensure compliance with the Act.
Overall, the investigation did not find any contravention of the Act. However, it highlighted certain shortcomings related to the CBSA’s contracting practices that could have had an impact on privacy. The findings stemming from this investigation are an opportunity to raise the awareness of all government institutions and improve privacy practices in the context of contracting.
Overview
In March 2024, after receiving a complaint, the Office of the Privacy Commissioner of Canada (OPC) launched an investigation into the Canada Border Services Agency’s (CBSA) contracting practices in relation to the development of the ArriveCAN application. The complainant alleged that the CBSA may be in contravention of sections 7 and 8 of the Privacy Act (the Act) if the resources contracted by the CBSA had access to, or had the potential to access, travellers’ personal information, without the necessary security clearances.
Subsequently, in a motion dated May 6, 2024, the Standing Committee on Government Operations and Estimates (the Committee) requested that the OPC investigate the work of all contractors and subcontractors who worked on ArriveCAN to determine whether the privacy and personal information of Canadians was adequately protected during the development of the app.
In light of the concerns raised, the OPC’s investigation assessed the CBSA’s compliance with the Act by examining its contracting practices in relation to ArriveCAN and the measures taken to mitigate privacy risks associated with the use of contracted resources.
Our review considered: (i) whether appropriate clauses, including security requirements, were included in the contracts and the associated task authorizations (TAs)Footnote 1 relating to ArriveCAN to ensure the protection of personal information, and whether these requirements were accurate and specific; (ii) the CBSA’s compliance with the security requirements established for ArriveCAN-related contracts, including vendor and contractor security screening; and (iii) whether appropriate security safeguards were implemented to protect personal information, including relevant administrative and technical controls.
Following our investigation, we made the following key findings:
- All ArriveCAN-related contracts that allowed access to personal information included appropriate clauses to describe the contract security requirements and specific safeguards to be implemented. Security Requirements Check Lists (SRCLs)Footnote 2 were completed to identify, among other things, the type and level of information that the contractors would require access to, and the security screening level(s) required for vendors and contracted resources. However, our investigation found issues regarding the accuracy and timeliness of certain security assessments. For instance, one SRCL was completed four years before the contract was awarded, a significant gap that could have undermined the accuracy and reliability of the security assessment. In another case, the SRCL included a document safeguarding capability (DSC)Footnote 3 which was subsequently deemed unnecessary 14 months later. This also calls into question the accuracy of the security assessment and the data upon which the assessment was based.
- The TAs identified the security requirements applicable to the tasks outlined, within the framework and scope of the overarching contracts. However, we noted that, in some cases, the task descriptions in the TAs were very broad, and did not specifically identify the name of the project or system that contractors would be working on. The OPC also finds it concerning that the TAs under which ArriveCAN-related work was carried out were, in some cases, authorized before the ArriveCAN project was known or identified. In our view, this practice prevents institutions from performing an adequate assessment of specific privacy and security requirements required for a given project.
- All vendors met the contract security requirements established by the CBSA (i.e., organization screening), and these requirements were met for the duration of their respective contracts.
- All 13 contractors that were granted access to the ArriveCAN production environment (where personal information was stored) had the required security status or clearance (as stipulated in their TA) before they began work for the CBSA. We found, however, that one contractor worked for a year and a half without an up-to-date security clearance as a result of a processing delay by the CBSA.
- Six of the 13 contractors were granted access to the ArriveCAN production environment for activities that did not require access to travellers’ personal information because the IT user role they were assigned enabled them to access this information. The OPC confirmed that these contractors did not exercise the permissions they were granted to access travellers’ personal information.
- We assessed whether key security controls were implemented by the CBSA to protect ArriveCAN data. Overall, we found that the CBSA implemented adequate administrative and technical safeguards in relation to the contractors’ activities. For instance, only CBSA-issued laptops were used by contractors to access the ArriveCAN production environment, and access to travellers’ personal information was protected through logically segregated environments with strict access controls.
- Finally, the OPC’s investigation revealed certain shortcomings in relation to procurement processes that may have had impacts on privacy, including procurement file documentation.
Despite the issues highlighted above, the OPC found no evidence to suggest that personal information collected through ArriveCAN was used or disclosed in contravention of the Act. We therefore find the complaint to be not well-founded. Nevertheless, going forward, the OPC expects that the CBSA will take the following steps when contractors perform work on its behalf:
- ensure that security requirements are rigorously and accurately assessed and completed within a reasonable time prior to contract award;
- ensure that TA task descriptions clearly and accurately define the projects or work to be performed to ensure that privacy and security requirements specific to those tasks or projects are accurately identified and assessed;
- proactively manage security clearances and renewal processes with rigour and strong oversight; and
- restrict permissions and access to what is strictly necessary.
The CBSA accepted the OPC’s recommendations and agreed with the overall objective of strengthening privacy and security practices within its contracting framework. The CBSA also indicated that it remains committed to ensuring that its policies and procedures uphold the highest standards of accountability, transparency and the protection of personal information. We share the CBSA’s response to these recommendations at paragraph 91 of this report.
Background
- The ArriveCAN app was designed to respond to the COVID-19 pandemic by digitizing the collection of traveller information and expediting the processing of travellers at the border. The app collected a range of health and travel information, including vaccination status, travel history, contact information, and information related to COVID-19 symptoms.Footnote 4
- The CBSA’s development of the ArriveCAN app began in March 2020, at the request of the Public Health Agency of Canada (PHAC) to carry out COVID-19 measures under a series of emergency orders.Footnote 5 The app was first launched on April 29, 2020, and enabled to run on three common platforms.Footnote 6 The use of the app became mandatory in November 2020, and evolved with changes to federal public health orders until the COVID-19 related travel orders were discontinued on October 1, 2022.
- Given the urgent need for IT professional services, and due to limited internal capacity, the CBSA relied extensively on contractors for ArriveCAN program delivery, including the development and maintenance of the app. The CBSA issued updates to the application after its launch through a total of 177 releases across the three platforms. These releases were driven by PHAC business requirements and Order in Council changes, as well as updates to the app to address fixes raised through IT support. See Annex A for a timeline of ArriveCAN major releases.
- From its launch in April 2020, to the end of the mandatory public health measures in October 2022, the CBSA reported to the OPC that over 29 million submissions were received for approximately 46 million travellers.Footnote 7 During this same period, border services officers manually entered information into CBSA systems for travellers who had not completed ArriveCAN submissions electronically. Overall, personal information for approximately 60 million travellers was entered into CBSA systems using both methods.
- While using the ArriveCAN app has not been mandatory since the COVID-19 travel restrictions were lifted, the optional Advance CBSA Declaration (digital customs and immigration declaration feature) within ArriveCAN remained in use, and to this day is still available for travellers to use to save time at the border.
- The app has generated significant scrutiny and public attention. Following reports from the Office of the Procurement Ombud (OPO)Footnote 8 and the Office of the Auditor General (OAG),Footnote 9 important gaps and weaknesses in procurement processes, controls, oversight and accountability were identified. Concerns were also raised regarding potential unlawful access to sensitive traveller personal information by contracted resources, thus prompting concerns about the safeguards implemented by the CBSA to ensure the protection of this information. Notably, the OAG’s review also found that some contracted resources did not have a security clearance, which potentially exposed the CBSA to an increased risk of security breaches.Footnote 10 The latter issue was considered in the OPC’s investigation, and our findings are explained at paragraph 55.
Complaint
- On March 7, 2024, the OPC received a complaint from an individual regarding the CBSA’s contracting practices, specifically highlighting that some contracted resources involved in the app development may not have had the appropriate/required security clearances. According to the complainant: “if any contractors or subcontractors lacking the necessary clearances had access to—or even, through the CBSA’s poor management and oversight, had the potential to access—travellers’ personal information, this would amount to a breach of sections 7 and 8 of the Privacy Act.” The OPC launched its investigation against the CBSA on March 19, 2024.Footnote 11
- Subsequently, in a motion dated May 6, 2024, the Committee requested that the OPC investigate privacy related aspects of the ArriveCAN app, including the work of all contractors and subcontractors to determine whether the privacy and personal information of Canadians was adequately protected.
Scope and Methodology
- Contracting with third-party service providers can introduce privacy risks for government institutions, particularly when access to government systems and to individuals’ personal information is required under the terms of a contract. These risks include the unauthorized access, use or disclosure of personal information by contractors, or the compromise of personal information that contractors are entrusted to store and safeguard.
- In this case, the contractors engaged by the CBSA only used CBSA-issued laptops to access the cloud platform where ArriveCAN was hosted, and at no time was CBSA or ArriveCAN information stored with contractors off-site; therefore, the OPC’s investigation focused on the contracting, administrative and technical controls implemented by the CBSA to mitigate against risks associated with contractors’ access to personal information collected through ArriveCAN and hosted in the cloud.
- The OPC’s investigation assessed the measures implemented by the CBSA to mitigate such risks, including the requirements to: (1) establish clear contractual agreements with appropriate clauses, including security requirements to ensure the protection of personal information, and ensuring that these requirements are accurate and specific; (2) comply with the security requirements established for the ArriveCAN-related contracts, which includes conducting organization and personnel security screening; and (3) implement appropriate security safeguards to protect personal information, including administrative and technical controls.
- The CBSA confirmed that it awarded a total of 25 contracts relating to ArriveCAN; however, the OPC’s investigation confirmed that only 9 (of the 25) contracts involved access to traveller data by contracted resources. Additionally, while a total of 61 TAs were issued under these 9 contracts, we confirmed that only 15 TAs involved access to traveller data. The majority of the 9 contracts reviewed by the OPC were not specific to ArriveCAN and had broader requirements (i.e., ArriveCAN was just one of many projects delivered under the contracts).
- The OPC’s investigation was informed by a review of relevant ArriveCAN contracts and TAs to determine whether the contractors that had access to the ArriveCAN production environment met the contract security requirements (i.e., they had the requisite security status or clearance at contract award and throughout the duration of the contract, including when accessing travellers’ personal information), and that the contractors only accessed personal information collected through ArriveCAN within the period of service of their respective TA, and for appropriate purposes.
- The OPC’s review covered the period from the application’s initial launch in April 2020, when it was first used to collect travellers’ personal information, to November 2022, shortly after the mandatory use of the app as part of public health measures ended. While the CBSA continued to use contracted resources for ArriveCAN-related work between November 2022 and May 2023, it confirmed that contractors were only engaged to support the mobile app in a test environment that did not require access to personal information, and that any requirements to access personal information were executed by government employees. The CBSA reported that after May 15, 2023, it relied exclusively on its employees to support ArriveCAN.
- The OPC’s investigation was also informed by written submissions and meetings with key CBSA stakeholders, including the CBSA’s Advanced Cyber Defence Centre which also provided us an IT demo. Additionally, we reviewed information submitted by Public Services and Procurement Canada (PSPC), which was the Contracting Authority for 8 of the 9 contracts, to better understand its role and responsibilities in relation to procurement and contract security.Footnote 12
- We also considered information submitted by the private sector organizations (vendors) that were awarded the contracts, and contacted the Royal Canadian Mounted Police (RCMP) in light of its ongoing ArriveCAN investigation, given the potential for overlap with the OPC’s review as it relates to Canadians’ privacy. At the time of writing of this report, the OPC had not received any information from the RCMP deemed relevant to our investigation.
Analysis
Issue: Did the CBSA authorize contractors to access personal information collected through ArriveCAN without the required security clearance, in contravention of the requirements of sections 7 and 8 of the Act
- In light of the concerns raised by the complainant and the Committee, this report examines the CBSA’s compliance with sections 7 and 8 of the Act, which outline the conditions under which personal information can be used and disclosed by government institutions.
- The Act aims to protect the privacy of individuals with respect to their personal information held by a government institution. This places a responsibility on institutions to ensure that reasonable safeguards are in place to protect personal information. While not explicitly required under the Act, safeguards are mandated by relevant Treasury Board Secretariat (TBS) privacy policy instruments that support the Act’s administration.Footnote 13 The implementation of safeguards helps to ensure that appropriate security controls are in place to protect information from both accidental and deliberate threats (e.g., unauthorized access, modification, disclosure, misuse, etc.).
- There are no provisions in the Act nor in TBS privacy policy instruments that prevent government institutions from using external contracted resources. Contractors can provide specialized skills and expertise that may not be readily available within the government’s existing workforce and can be an efficient, cost-effective solution for short-term staffing needs. However, outsourcing can raise additional privacy risks, particularly if contractors require access to government information or assets. For instance, the handling of sensitive personal information by third parties can increase exposure to risks such as unauthorized access, misuse or unlawful disclosure of personal information, which can lead to data breaches.
- It is therefore important for institutions to consider the privacy implications carefully when contracting out their activities and take steps to ensure that appropriate safeguards are implemented to mitigate the risks associated with outsourcing and to protect personal information that contractors have access to.Footnote 14 The OPC’s investigation examined the measures implemented by the CBSA to mitigate against such risks. Our findings are outlined in the sections below.
Sub-issue 1: Did the ArriveCAN contracts and TAs contain appropriate clauses to ensure the protection of travellers’ personal information that contractors had access to
- To mitigate the privacy risks associated with the use of contracted resources and ensure the protection of personal information that contractors may have access to, government institutions are required to establish clear contractual agreements with appropriate clauses, including security requirements.Footnote 15
Did contracts and TAs contain the required security clauses?
- As the client department, the CBSA was responsible for defining its business and operational requirements and ultimately managing the lifecycle of the contracts. The Contracting Authority was responsible for planning and organizing the acquisition of professional services for the client.Footnote 16
- PSPC was the Contracting Authority for 8 of the 9 contracts that involved access to travellers’ personal information. The OPC confirmed that PSPC awarded 5 of these contracts under supply arrangementsFootnote 17 to provide the CBSA with access to professional resources needed to support a variety of technology-related initiatives on an “as and when required basis”. The remaining 3 contracts were awarded by PSPC non-competitively. For all contracts, PSPC submitted to us that it consulted the client (CBSA) to understand their requirement(s) and, as part of developing the procurement strategy, determined that these procurement methods were appropriate to meet the client’s needs.Footnote 18 The CBSA was the Contracting Authority for the single outstanding contract and it was also issued under a supply arrangement.Footnote 19 We note that the majority of these contracts were not established specifically for ArriveCAN.
- A contract will include clauses relating to security requirements when access to protected or classified information, assets or sites is required (See Annex B for a description of the security levels for sensitive government information and assets). Security requirements are established by the client department (in this case, the CBSA) and aim to mitigate privacy and security risks when government functions or services are performed under contract.
- The OPC’s investigation confirmed that all 9 contracts had clauses to describe applicable security requirements. For instance, these usually include the specific screening level that the vendor must hold, the specific security status or clearance that contractors are required to have to access information or assets, and any other security requirements stipulated by the client.Footnote 20
- For contracts with TAs (that authorized contractors to be engaged on an “as and when required basis”), it was the responsibility of the client, specifically the Technical/Project Authority within the CBSA, to ensure that TAs were issued in accordance with the TA process set out in the contract,Footnote 21 and also that they aligned with the scope and framework of the overarching contract, including the Statement of Work.Footnote 22 Our review confirmed that the TAs included details on the tasks/activities to be performed and other specific information, such as the security status or clearance required of contracted resources for the tasks, and that, overall, they aligned with the scope of work and security requirements identified in the contracts.Footnote 23 However, we found that certain TA task descriptions were broadly framed and lacked specific details, such as the name of the project or system that contractors would be working on. The OPC’s observations are outlined in the section below.
Were security requirements accurate and specific?
- Government institutions are required to identify and document security requirements for all contracts and TAs. These requirements are determined based on a number of factors, including the sensitivity of information to which individuals will require access, and the location or type of work to be performed, and must be assessed and specified at the beginning of the procurement process.Footnote 24 Our review confirmed that personal information collected through ArriveCAN was categorized as Protected B.Footnote 25
- The SRCL is the tool used by federal institutions to assess and identify the levels of security required to safeguard government information and assets throughout the contract’s duration. The SRCL includes a brief description of the work to be performed and specifies what information the contractors will require access to (e.g., protected and/or classified), and the categorization (e.g., Protected B) or classification (e.g., Secret) level of that information .The SRCL also specifies the required personnel security screening level (e.g., reliability status), and establishes the vendor security screening level and any additional required safeguards (e.g., if the vendor is required to store protected and/or classified information on its site or premises, or use its own IT systems to process or store information).Footnote 26
- The OPC examined the SRCLs for all 9 contracts to confirm the contract security requirements, and specifically, the levels of organization and personnel security screening status or clearance that were required. We also examined the 15 TAs that were issued under these contracts to confirm the security screening level requirements identified by the CBSA for the resources.Footnote 27
- Our investigation confirmed that the SRCL was completed for all 9 contracts. However, we noted that in one case, the SRCL was completed for a contract 4 years before the contract was awarded.Footnote 28 While there are no current restrictions on the time between the signing of a SRCL and awarding of a contract, we are concerned that such a significant passage of time could impact the accuracy and reliability of the security assessment, particularly if the security landscape changes and/or the data relied upon for the assessment is outdated by the time the contract is awarded. This also raises privacy concerns about the relevance of the initial assessment, which could potentially lead to ineffective or insufficient privacy and security measures when work is finally carried out under the contract.
- Our investigation also revealed that the SRCL for another contract identified a DSCFootnote 29 that was subsequently deemed unnecessary 14 months later. This also calls into question the accuracy of the security assessment and the data upon which the assessment was based.
- With respect to the contracts’ Statements of Work (SOWs), the CBSA submitted that they kept these broad on purpose to allow for flexibility depending on the CBSA’s requirements. TAs were then issued as needed when resources were needed to complete the work, based on the tasks/activities and deliverables defined by the CBSA, and consistent with the scope and framework of the overarching contract. The CBSA explained that it provided direct oversight and managed contractors’ work assignments and deliverables.
- However, while we found that the TAs aligned with the scope of the contracts and security requirements set out in these contracts, we noted that in some cases, task descriptions for TAs were broad and did not specifically identify the name of the project or system that a contractor was working on. Such task descriptions can raise privacy risks, particularly when tasks associated with projects are not known or explicitly identified when the TA is authorized/issued. For instance, in ArriveCAN, we note that there was a TA issued two years before work on the app even began.Footnote 30 Consequently, at the time of TA issuance, any specific privacy or security requirements related to ArriveCAN were not known (e.g., that access to travellers’ personal information would be required) nor specifically assessed by the CBSA.
- These observations underscore the importance of a thorough SRCL process and the need to identify the actual projects or tasks to be performed under the terms of a contract, including TAs, to ensure that security requirements are accurately assessed and identified. Completing such assessments within a reasonable time prior to contract award is key to achieve this objective. A failure to accurately assess security or safeguarding requirements may, in other circumstances, result in insufficient security measures and increase the risk of privacy breaches, particularly if these requirements are underestimated.
Sub-issue 2: Did the CBSA comply with security requirements for ArriveCAN-related contracts and TAs
- When establishing contracts that involve the handling of personal information, government institutions must exercise due diligence to ensure that contract security requirements are respected. This includes ensuring that the vendors and contractors meet the contract security requirements, and that personal information is accessible only to authorized individuals, for appropriate purposes. In addition, security requirements must be met throughout the entire duration of the contract.
Organization screening
- In order to obtain a security status or clearance for their resources to access protected or classified information, assets and work sites, vendors must obtain the required organization security screening before the contract is awarded.Footnote 31 The two types of organization screenings relevant to the OPC’s review include Designated Organization Screening (DOS), and Facility Security Clearance (FSC).Footnote 32
- Based on the submissions received from both PSPC and the CBSA, we are satisfied that the vendors met the contract security requirements that were established by the CBSA in 8 (of the 9) contracts and confirmed that these requirements were met for the duration of the respective contracts.
- Our investigation revealed that one vendor did not hold a DOS with approved DSC at the level of Protected B, as required by the contract SRCL.Footnote 33 The OPC questioned PSPC, given its role as the Contracting Authority, to understand why the contract was awarded to the vendor in that case, since the security requirements were not met.
- PSPC confirmed that, while the vendor in question did not hold a DOS at contract award, they held a FSC, which is in effect a higher clearance, and they were therefore eligible for this contract. While the contract also required a DSC, PSPC reported that this safeguarding capability was not ultimately required and that the CBSA requested an amendment to the contract security clause and SRCL to remove it as a requirement. PSPC also reported that a DSC can be initiated and confirmed after contract award – i.e., it is not necessary to hold a DSC to be awarded the contract.
- In this case, we agree that a DSC (site-specific clearance required for safeguarding sensitive information at a specific location) was not required for this vendor because no personal information collected through ArriveCAN was stored outside of the CBSA’s infrastructure. We also confirmed that the contract was amended 14 months after it was awarded to remove the requirement for a DSC.
- In light of the above, the OPC is satisfied that the vendors met their respective contract security requirements. Nevertheless, we find it concerning that a safeguarding requirement (DSC) was identified at the requirement definition stage of one contracting process and was subsequently deemed unnecessary 14 months later.
Personnel security screening
- Personnel security screening is an important risk mitigation measure, and it must be completed, confirmed and documented before a contractor can commence work and is granted access to personal information. It provides reasonable assurance that the contractor can be trusted to access government information and assets and can reliably conduct their work duties. It is a key security control to protect information and assets, and, as per the Directive on Security Screening, is a requirement for contracts where there is a need to share or provide access to sensitive information and assets, including IT systems and facilities.
- The OPC’s investigation confirmed, through a review of documentation and a sampling of audit logs, that a total of 13 contractors had access to the ArriveCAN production environment during the period under review, and only 7 of these 13 contractors exercised the permissions they were granted to access travellers’ personal information to achieve their work objectives.Footnote 34 We confirmed that the remaining 6 contractors were granted access to the production environment for activities that did not require access to personal information (e.g., maintenance, code updates, etc.). While these contractors did not access travellers’ personal information to perform their duties (nor were they required to), the IT user role they were assigned nevertheless enabled them to access this information.Footnote 35
- The OPC’s investigation examined whether all 13 contractors met the security screening requirements of their respective TAs. We requested documentation from the CBSA to validate the security screening status or clearance of the 13 contractors that were identified in the TAs and had access to the ArriveCAN production environment.Footnote 36 Following our review of each contractor’s security status or clearance against the period of service for their TA, we are satisfied that all 13 contractors met the security requirements of their respective TA when it was issued, and for the duration of the TA period of service, with the exception of one contractor.
- The OPC’s investigation revealed that the security clearance (Secret level) for this contractor was valid when they began work in October 2018; however, it expired in January 2019.Footnote 37 While the CBSA confirmed that a request for update was submitted in August 2018, the contractor’s clearance was not updated until October 2020 due to delays in the screening process. As such, this contractor continued doing work for the CBSA for over 18 months without a valid security clearance.
- The CBSA disagreed with the OPC’s position that the contractor worked “without a valid clearance”. It submitted that, barring evidence of a security risk that would need to be addressed, employees and contractors can continue to carry out their duties while their screening is being updated. The CBSA also stated that, although the TBS Standard on Security Screening (which was in effect at the time) required screening to be updated in accordance with established update cycles (e.g., every 10 years for Secret), the Standard did not require any other non-screening related action to be taken between the time a clearance is required to be updated and the granting of the updated clearance. The CBSA reported that there were no privacy and security risks relating to this contractor, as they had been properly screened previously, and their screening was later updated with no issue.
- According to PSPC, if a clearance update for a contractor is not completed on time, either because the vendor failed to submit their update request in a timely mannerFootnote 38 or because additional verifications or a security screening interview were required, it is for the client (CBSA) to make the decision as to whether it wishes to remove the resource from a contract. In cases where a contractor’s security clearance is set to expire before the end of the contract, some clients will require that the update process be completed before the contract is awarded, but others may allow the resource’s security clearance to be updated while the contract is underway, provided the update is completed before the expiry date. The client department is expected to work with their contractors to ensure that they are submitting update requests in a timely manner.
- Institutions have a duty to ensure that contractors’ security clearances are updated prior to the end of their validity period,Footnote 39 as contractors’ personal circumstances may change (e.g., divorce, arrest, criminal conviction, etc.) during the course of a contract which could affect their status or clearance. Such a change may also result in some contractors potentially engaging in behaviours that could result in a compromise to security or personal information held by the institution. The purpose of an update is to reassess individuals’ reliability or loyalty, taking into account changes in their personal circumstances since the time they were last granted a security status or clearance. Updates focus on determining whether, in light of the duties being performed, any personal changes pose a potential security risk and affect eligibility to hold a security status or clearance.
- While the CBSA submitted that there were no privacy and security risks relating to this contractor, it did not demonstrate how it assessed the risks or what steps it took to mitigate them. Rather, the CBSA stated that the contractor had been properly screened prior to starting work on the project, and that their screening was later updated without any issue. The CBSA also failed to explain why the clearance update process took so long. If the delays were caused by the contractor, we would expect for consideration to have been given to the administrative cancellation of the individual’s security status or clearance, as provided under the TBS Standard on Security Screening.Footnote 40 The CBSA could have also temporarily revoked the contractor’s access to the ArriveCAN production environment where travellers’ personal information was stored until the clearance renewal process was completed.
- The OPC therefore finds that the CBSA exposed itself to increased and unnecessary privacy risks by authorizing the contractor to have access to the ArriveCAN production environment without meeting the contract security requirements (i.e., an up-to-date clearance) for over 18 months. In our view, the period that the contractor worked without a valid clearance was driven by the CBSA’s operational needs only and was not the result of a strategic risk-based decision process. In fact, it was fortunate that there were no privacy breaches during that prolonged period, but that may not always be the case.
- Notwithstanding the above, the OPC found no evidence to suggest that travellers’ personal information was accessed, misused or disclosed without authorization by this contractor, or any of the other 12 contractors, and therefore we did not find that there was a contravention of sections 7 or 8 of the Act.
- This investigation nonetheless underscores the value and importance of security screening and monitoring compliance with contract security requirements throughout the lifecycle of a contract. Client departments should reconfirm clearance status when necessary to account for any changes to the security status of individual resources.Footnote 41 Even if it did not happen in this case, a failure to monitor and ensure compliance with contract security requirements can put personal information and assets at risk of unauthorized access, use or disclosure.
- It is therefore the OPC’s expectation that, going forward, the CBSA will proactively manage security clearances and renewal processes with rigour and strong oversight.Footnote 42 While security screening updates should be completed before the expiry of a contractor’s security status or clearance, at a minimum, we expect institutions to be able to demonstrate how they assessed or mitigated risks if they decide to maintain access to personal information for a contractor whose security clearance has expired. We recognize that a risk-based approach is necessary to strike the right balance between operational needs and the privacy risks associated with allowing contractors to continue working without a valid security status or clearance.
- On this point, the OPC notes that suppliers (vendors) also have a responsibility in the security clearance process. Their obligations include submitting security screening requests for their personnel if access to protected or classified information is required, and submitting requests for updates and upgrades when required.Footnote 43 In this case, while the request for renewal of the contractor’s security clearance was submitted approximately 6 months before their clearance expired, we note that this may have also contributed to the situation described above. The Contract Security Program (CSP) recommends that organizations submit update requests for their resources at least one year in advance for Secret clearances, which is the level the contractor required.
- The OPC’s investigation also considered a finding made by the OAG, namely that some contracted resources involved in the ArriveCAN project did not have a security clearance.Footnote 44 We sought representations from the CBSA on this point and confirmed that the work conducted by the contractors referenced in the OAG report did not involve access to travellers’ personal information or to the actual ArriveCAN application code. That said, the CBSA confirmed that, while it had identified 4 specific resources to conduct that work, the vendor later substituted them without approval, which was a breach of its security obligations (i.e., the resources approved in the TA to do the work were not necessarily the ones who ended up performing the work).Footnote 45
- While we acknowledge that vendors have a responsibility to adhere to the security requirements of the contracts they enter into, we note that the CBSA is also accountable for TA oversight and management. Indeed, it is not clear to the OPC how the CBSA fulfilled its obligations as Project Authority related to managing the work assignments for these contractors and monitoring task performance and delivery. Further, while the work noted above did not involve access to any personal information, the lack of TA oversight could have exposed the CBSA to increased and unnecessary privacy risks in other circumstances.
Sub-issue 3: Did the CBSA implement adequate safeguards to protect personal information collected through ArriveCAN that was accessed by contractors
- The ArriveCAN app was developed and hosted on the Amazon Web Services (AWS) cloud platform, through the provisions of the Shared Services Canada (SSC) Cloud Framework Agreement.Footnote 46 The cloud platform is designed, maintained, and operated by the CBSA, and has a “Protected B, Medium Integrity/Medium Availability” (PBMM) security control profile for cloud-based services.Footnote 47 This means that the highest level of information that it can store is Protected B, which is the level of classification of personal information collected through ArriveCAN.Footnote 48
- While it was beyond the scope of the OPC’s investigation to conduct an exhaustive review of safeguards other than contractual security requirements, we nevertheless examined whether the CBSA implemented security controls to protect travellers’ personal information from unauthorized access, disclosure, or misuse in general, and by contracted resources in particular.Footnote 49
- As detailed below, the OPC’s investigation found that the CBSA implemented adequate administrative and technical controls to protect Canadians’ personal information in ArriveCAN and to mitigate risks associated with contractors’ access to this information. However, we are concerned that all 13 contractors were granted the same user roles/permissions to access the production environment, even though 6 contractors did not require access to the personal information stored therein.
Administrative controls
- Administrative controls include the policies and procedures to manage security within an institution, including procedures associated with the use of contracted resources. The OPC’s investigation considered procedures associated with the (i) onboarding of contractors, (ii) contractors’ use of CBSA-issued laptops, (iii) compliance with IT standards and accepted frameworks, and (iv) cyber security governance.
Onboarding of contractors
- As part of its due diligence, the CBSA’s onboarding process for ArriveCAN included specific steps to ensure that only authorized vetted contractors were granted access to the production environment (where traveller data is stored). These steps included security clearance validation before contractors commenced work, authorizing local area network (LAN) accessFootnote 50 to the CBSA network, and validation by the CBSA’s cloud team prior to creating a CBSA AWS account based on the business objectives and role of the contracted resource. Contractors were also asked to acknowledge and agree to the CBSA “terms of use” for electronic resources and the AWS cloud platform policy, which set out the responsibilities of authorized users and the acceptable and unacceptable uses of accessed resources.
Use of CBSA-issued laptops and storage infrastructure
- The contractors used a CBSA issued laptop to access the AWS cloud platform where ArriveCAN was hosted. At no time was ArriveCAN information stored with contractors off-site. This measure allowed the CBSA to mitigate potential additional risks of contractors using their own equipment or hosting infrastructure.
Compliance with IT standards and accepted frameworks
- The CBSA’s cloud platform environment meets the cyber security controls and architecture requirements established by the Government of Canada (see Government of Canada Cloud Guardrails).Footnote 51 The platform was also assessed against the Communications Security Establishment (CSE) IT security framework ITSG-33.
- In addition, the CBSA implemented industry-standard security measures to monitor the AWS cloud platform and ArriveCAN app to ensure adherence to its internal policies and guidelines,Footnote 52 and to ensure alignment with the TBS Directive on Security Management, which requires institutions to implement minimum security controls to protect IT systems from unauthorized use and compromise.
Cyber Security Governance
- In April 2024, the CBSA’s Cyber Security Directorate (CSD) was formally created to centralize all cyber and IT security functions. Within this Directorate, there is an Advanced Cyber Defense Centre (ACDC) which is responsible for monitoring and responding to security incidents. The team includes analysts who monitor the AWS platform on which ArriveCAN operates.
- Additionally, the CBSA’s CSD has direct lines of communication with the Canadian Centre for Cyber Security (CCCS), the Government of Canada’s enterprise Security Operations Centre (SOC), and SSC on all files and for incident alerting and response. The CBSA reported that part of the planned evolution of the CSD’s functions is to continue to mature the cyber security functions into a fulsome CBSA SOC, which, in our view, should further enhance the CBSA’s security posture and incident response capabilities.
Technical controls
- Technical controls include the system-based controls that leverage technology that protect an institution’s IT systems and mitigate risks associated with access to government information or assets. Such controls include architectural safeguards, encryption, user access controls, and monitoring for unauthorized or malicious activities.
App design and architectural safeguards
- The ArriveCAN cloud platform was logically segregated into three environments – development, testing, and production. During the development of the app, all of the development, testing and validation activities were conducted in non-production environments using non-production data (e.g., randomized data, such as fictitious names, dates of birth, etc.). Therefore, no production data (travellers’ personal information) was used at any stage during the development or testing of the ArriveCAN app. We found the use of logically segregated environments with strict access controls to be effective in limiting personal information collected through ArriveCAN from exposure.
Encryption
- Encryption protects the confidentiality of information by making it unreadable to unauthorized individuals who may access it.
- The OPC confirmed that the CBSA implemented CCCS approved, robust encryption protocols for data both in transit and at rest,Footnote 53 which enhanced its defence against unauthorized use but also supported compliance with the Government of Canada’s cyber security standards.Footnote 54
User access controls
- The CBSA’s cloud platform security framework uses identity and access management (IAM) and role-based access control (RBAC) to ensure that access is only provided to users (CBSA employees and contractors) for the specific content and services required to carry out their duties.Footnote 55 Specifically, user access roles on the cloud platform are defined by job type (e.g., software developer, security, administrator, etc.), and user roles are created per role and per environment to provide users with the permissions needed to carry out their role, in line with defined business objectives.Footnote 56
- The OPC confirmed that contractors’ access to personal information in ArriveCAN was related to two specific purposes: (i) production support (personal information was accessed if there was an ArriveCAN error that required attentionFootnote 57), or (ii) processing Access to Information and Privacy (ATIP) requests.Footnote 58
- Overall, we found that the implementation of IAM and RBAC measures (e.g., granting the “least privileges” required for access based on a user’s roleFootnote 59) effectively mitigated privacy risks associated with access to travellers’ personal information, including access by contractors. By default, the role that was assigned to contractors did not allow them to directly extract personal information from the production environment (approved processes were required to extract personal information indirectly—e.g., to run commands such as bulk copying the dataset), and access was tightly controlled and monitored.
- However, while contractors were not able to directly extract personal information from the production environment,Footnote 60 we are still concerned that 6 of the 13 contractors had access to travellers’ personal information that was not required for their work duties. This is because all 13 contractors were granted the same user roles/permissions.Footnote 61
Monitoring and auditing processes
- The CBSA conducts audit loggingFootnote 62 to capture user actions taken on the platform. It also has monitoring capabilities for threat detection (analyzing network traffic and account activities to identify unusual or unauthorized behaviour). The CBSA’s threat detection service provides automated alerts on potential security issues or data breaches and checks for anomalies in data access to allow the CBSA to detect and respond to threats promptly, including insider threats.
- As part of its representations to the OPC regarding its processes, the CBSA’s Advanced Cyber Defence Centre gave us an IT demo. Overall, we found that the CBSA employed appropriate auditing and monitoring tools to detect anomalous activities, including the activities of contractors.
Other
Procurement practices that may impact privacy
- The OPC contacted the vendors that were awarded the contracts in question in order to validate certain representations we received from the CBSA (e.g., to confirm which contractors had access to personal information in ArriveCAN) and to inform our assessment of the CBSA’s compliance with the Act. Based on the information submitted by the vendors, the OPC made certain observations that relate to procurement practices that may have an impact on privacy.
- Of note, the OPC found that some vendors were generally unaware of the work and/or specific projects that their contracted resources were assigned to work on, because in some cases, resources were provided as a “staff augmentation service” and the work was directed and managed exclusively by the CBSA. Vendors also reported that the work to be performed by their resources under TAs was often broadly worded, including task descriptions not explicitly linked to ArriveCAN. They therefore noted that it was difficult for them to determine which TAs were associated to ArriveCAN, or whether any specific tasks (such as access to personal information by contracted resources) were related to ArriveCAN. As a result, vendors had difficulty confirming which resources worked on ArriveCAN or had access to travellers’ personal information.
- These observations align with the OPC’s findings during the investigation. To mitigate privacy risks, it is important for institutions to identify the projects or work to be performed under the terms of a contract so that vendors can also meet their obligations when their employees are provided access to personal information.Footnote 63
Documenting security screening status
- Documenting security screening status is used to demonstrate that a contractor has been vetted and authorized to access assets, including personal information, and it creates a clear audit trail for accountability in the event of a privacy or security breach. It is also a TBS Directive requirement,Footnote 64 and important for facilitating management oversight and audit.
- As noted at paragraph 44, the OPC requested documentation from the CBSA to validate the security screening status or clearance of the 13 contractors that had access to the ArriveCAN production environment. While the CBSA produced documentation to demonstrate the validity of the security screenings, it confirmed that it did not include the required supporting records in the procurement files to demonstrate the successful transfer of two contractors’ security clearances.
- As the CBSA acknowledged, contracted personnel should have a valid security clearance at the required level; in addition, where applicable, there should be documentation in the procurement file to show the successful transfer or duplication of the individual’s security clearance. We note that this was not done in these two cases. While no privacy breach occurred, a lack of rigour in this respect can create risks for privacy, particularly if it hinders an institution’s ability to demonstrate compliance with security requirements related to access to personal information.
Findings and Conclusions
- The OPC’s investigation assessed whether the CBSA was compliant with the requirements of sections 7 and 8 of the Act when it authorized contractors to access personal information in ArriveCAN. We examined the measures implemented by the CBSA to mitigate against the risks associated with third party access to personal information stored in the ArriveCAN production environment, including ensuring that: 1) relevant contracts and TAs contained appropriate provisions to address privacy obligations and security requirements, 2) that it ensured compliance with security requirements established for the contracts and TAs, and 3) that adequate IT security safeguards were implemented to protect personal information against unauthorized access, use or disclosure.
- Overall, the OPC is satisfied that the contracts included appropriate clauses to describe the contract security requirements and the specific safeguards to be implemented to ensure the protection of personal information. The CBSA also assessed and documented contract security requirements through the completion of SRCLs. However, our investigation highlighted deficiencies in terms of the timeliness and accuracy of certain SRCLs, which raises concerns about the precision of the initial security assessments and could potentially lead to ineffective or insufficient privacy and security measures.
- The OPC’s review of the TAs issued under the contracts found that they respected the framework of the contracts, including the security requirements identified. However, we note our concerns that certain TA task descriptions were very broad and did not specifically identify the name of the project or system that contractors would be working on.
- With respect to security screening, the OPC is satisfied that vendors met the security requirements (i.e., organization screening) established by the CBSA for their respective contracts, and that these requirements were met for the duration of their contracts. We also found that the 13 contracted individuals that had access to the ArriveCAN production environment met the security requirements of their respective TAs before they began work for the CBSA.
- However, we did find that the CBSA exposed itself to increased privacy risks by authorizing access to the ArriveCAN production environment to a contractor with a lapsed security clearance for a prolonged period.
- The OPC’s review of the CBSA’s administrative and technical controls found that, overall, traveller data was protected by adequate IT safeguards in relation to contractors’ activities. The measures implemented by the CBSA during the development and deployment of the ArriveCAN app, including having logically segregated environments with strict access controls and the use of CBSA-issued laptops, were effective in limiting ArriveCAN data exposure and mitigating privacy risks.
- Despite the issues highlighted above, the OPC’s investigation found no evidence to suggest that personal information in the ArriveCAN production environment was used or disclosed in contravention of the Act. We therefore find the complaint to be not well-founded.
- Nevertheless, we shared with the CBSA our expectations and recommendations going forward to mitigate privacy risks associated with contracting out its activities. The CBSA agreed with the OPC’s recommendations and the overall objective of strengthening privacy and security practices within its contracting framework. The CBSA also indicated that it remains committed to ensuring that its policies and procedures uphold the highest standards of accountability, transparency and the protection of personal information.
- The CBSA’s responses to the OPC’s recommendations are detailed below:
- Ensure that the assessment of security requirements is completed within a reasonable time prior to contract award to mitigate risks associated with outdated or inaccurate data; the security requirements should be rigorously assessed and accurately identify the sensitivity of information and the safeguards that are required to execute the contract.
The CBSA acknowledged the importance of ensuring that all security requirements are accurately assessed and completed prior to the award of any contract. The CBSA noted that it continues to strengthen its contracting framework to ensure that appropriate security controls are in place before contract initiation. Tools, processes and procedures have already been reviewed and implemented to enhance openness, transparency and fairness in procurement, which also contribute to safeguarding privacy and personal information throughout the contracting lifecycle. - Describe the projects or work to be performed under TAs clearly and accurately, which is key to ensuring that the corresponding privacy and security requirements are properly assessed (based on factors such as the sensitivity of information and the location or type of work to be performed).
The CBSA agreed that TAs must clearly define the scope of work to ensure that all privacy and security requirements are properly identified and assessed. The CBSA noted that the recommendation aligns with past and current efforts made by the CBSA to address risks in its procurement process. - Manage security clearances and renewal processes proactively and with rigour and strong oversight to mitigate against potential privacy risks related to contractors’ access to personal information; at a minimum, this should include the implementation of a risk-based approach to assess contractors’ continued eligibility to access personal information in cases where clearances may not be valid or up-to-date.
The CBSA acknowledged the importance of rigour and strong oversight in security clearance renewal processes. The CBSA indicated that it will work with PSPC’s Contract Security Program to ensure that any screenings that are set to expire during the contract validity period are followed-up on with the supplier’s Company Security Officer, and that criteria are in place for the CBSA to review continued eligibility to access personal information in cases where clearances may not be up-to-date. - Restrict permissions and access to what is strictly necessary.
The CBSA reported that it is committed to further strengthening its access management practices to ensure that users, including contractors, are provided only the permissions necessary to perform their duties. The CBSA also stated that it is actively working toward establishing RBAC measures for other systems, exploring the feasibility of implementing restricted contractor accounts, and reviewing options to increase the frequency of access reviews and certification processes to every six months for all contractors, regardless of their role. In instances where elevated access privileges are required, the CBSA noted that it will continue to ensure that such access is granted only on an exceptional basis, for the minimum duration necessary, and that it remains subject to regular review and certification.
- Ensure that the assessment of security requirements is completed within a reasonable time prior to contract award to mitigate risks associated with outdated or inaccurate data; the security requirements should be rigorously assessed and accurately identify the sensitivity of information and the safeguards that are required to execute the contract.
- The ArriveCAN app played a key role in helping the CBSA and public health authorities to respond to an extraordinary public health crisis. That said, the development of the app also raised important questions about privacy during a pandemic,Footnote 65 which highlights the importance of striking a balance between urgency, robust contracting practices, and safeguards to ensure the protection of Canadians’ personal information.
- The OPC acknowledges the important steps the CBSA has taken to strengthen procurement practices to ensure it follows Government of Canada contracting rules, as a result of a number of reviews into procurement and contract management related to ArriveCAN. However, the OPC’s investigation underscores the need for more direct oversight and monitoring to ensure compliance with contracting processes that can have a direct impact on privacy and the protection of personal information.
- There is a strong nexus between contracting and privacy. Contracts serve as the legal framework to define how personal information will be handled and safeguarded, which is crucial for government outsourcing and to ensure compliance with the Act. The findings stemming from this investigation are an opportunity to raise the awareness of all government institutions and improve privacy practices in the context of contracting.
Annex A: ArriveCAN major releases
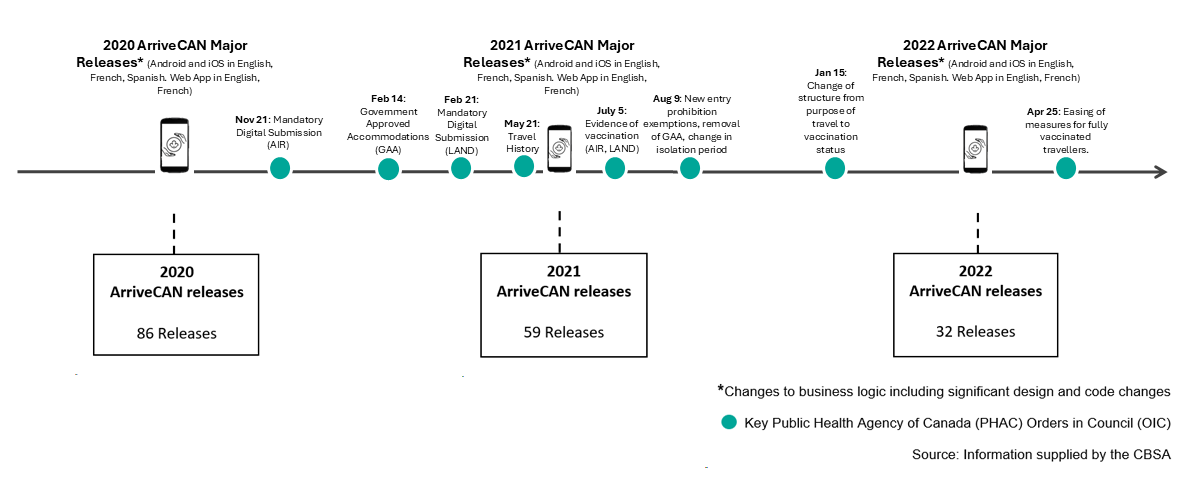
Text version of Figure 1
2020 ArriveCAN releases
86 Releases
- 2020 ArriveCAN Major Releases* (Android and iOS in English, French, Spanish. Web App in English, French)
- Nov 21: Mandatory Digital Submission (AIR)
2021 ArriveCAN releases
59 Releases
- 2021 ArriveCAN Major Releases* (Android and iOS in English, French, Spanish. Web App in English, French)
- Feb 14: Government Approved Accommodations (GAA)
- Feb 21: Mandatory Digital Submission (LAND)
- May 21: Travel History
- July 5: Evidence of vaccination (AIR, LAND)
- Aug 9: New entry prohibition exemptions, removal of GAA, change in isolation period
2022 ArriveCAN releases
32 Releases
- 2022 ArriveCAN Major Releases* (Android and iOS in English, French, Spanish. Web App in English, French)
- Jan 15: Change of structure from purpose of travel to vaccination status
- Apr 25: Easing of measures for fully vaccinated travellers.
* Changes to business logic including significant design and code changes
Key Public Health Agency of Canada (PHAC) Orders in Council (OIC)
Source: Information supplied by the CBSA
Annex B: Security levels for sensitive government information and assets
| Security level | Information / Asset | Organization screening | Personnel screening |
|---|---|---|---|
| Classified | Top Secret: Applies to information or assets that, if compromised, could cause exceptionally grave injury to the national interest. | Facility security clearance (Top Secret): Allows an organization to send appropriately security screened personnel with a need-to-know to restricted work sites to access protected and classified information and assets. |
Security clearance (Top Secret): Required by an employee working on a sensitive government contract to access classified (Top Secret) information and assets. An employee with a security clearance may also access protected information. |
| Secret: Applies to information or assets that, if compromised, could cause serious injury to the national interest. | Facility security clearance (Confidential or Secret) | Security clearance (Secret):Required by an employee working on a sensitive government contract to access classified (Secret, Confidential) information and assets. An employee with a security clearance may also access protected information. | |
| Confidential: Applies to information or assets that, if compromised, could cause injury to the national interest. | |||
| Protected | Protected C: Applies to information or assets that, if compromised, could cause extremely grave injury to an individual, organization or government. | Designated organization screening (DOS): Allows an organization to send appropriately security screened personnel with a need-to-know to restricted work sites to access protected information and assets. | Enhanced reliability status: Required by an employee working on a sensitive government contract to access Protected C information and assets. |
| Protected B: Applies to information or assets that, if compromised, could cause serious injury to an individual, organization or government. | Reliability status: Required by an employee working on a sensitive government contract to access Protected A or Protected B information and assets. | ||
| Protected A: Applies to information or assets that, if compromised, could cause injury to an individual, organization or government. | |||
| (Source: Adopted from PSPC’s Levels of Security) | |||
- Date modified:

