Remote access: Opening the door to your personal information

Read more

Read more

Read more

Seniors are no different than most. They are on the Internet every day making purchases and researching information, but they do remember a time when going to the store or library was as simple as walking in, getting what you wanted and heading out the door. The only footprints they left were in the snow.
Read more
Smart phones offer many benefits, including convenience and easier communication. Many people feel they can’t live without them, and use their devices for banking, shopping, paying bills, account verification and to access social media.
Read more
Smartphones and other mobile devices make it easy to connect and share.
Read more
March is Fraud Prevention Month across Canada. The Office of the Privacy Commissioner of Canada would like to encourage Canadians to be aware of all the ways criminals can obtain your personal information and steal your identity.
Read more
In a previous blog post we introduced the topic of cryptography, which is a key tool for keeping information secure and private. We used the example of a relatively simple symmetric encryption scheme where the encryption and decryption keys are the same.
Read more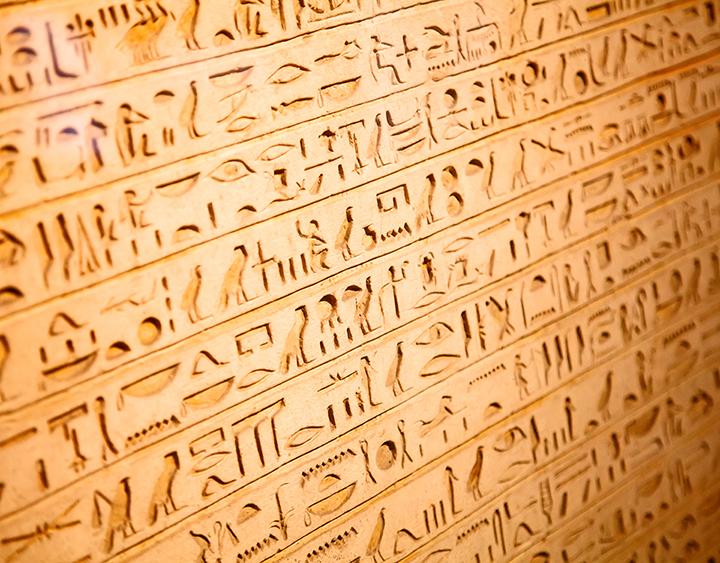
Individuals and organizations have long had a need to protect secrets from prying eyes. One way in which we protect those secrets is through the use of cryptography, from the Greek kryptós, meaning "hidden” or “secret" and graphein, meaning "writing". Early forms of cryptography were used by the ancient Egyptians, Greeks and Romans.
Read more
As the year comes to a close, the Office of the Privacy Commissioner of Canada would like to encourage all Canadians to keep privacy top of mind as they contemplate their New Year’s Resolutions.
Read more
Traditionally, we have logged into online systems using a username and password. These credentials are often being compromised, however, when databases containing them are breached or we are tricked into providing the information to fraudulent individuals or websites (often through phishing or other social engineering attacks). Once these credentials are compromised, attackers can use them to log into the associated online services. Even worse, because people often reuse their usernames and passwords, the attackers can access multiple services.
Read moreShowing items 1 through 10 of 36.