Joint investigation into a data breach at 23andMe by the Privacy Commissioner of Canada and the UK Information Commissioner
PIPEDA Findings # 2025-001
June 20, 2025
Overview
In October 2023, 23andMe Inc. (“23andMe”), a company that provides direct-to-consumer genetic testing and ancestry services to individuals globally, confirmed a data breach that affected almost 7 million of its customers. Given the scale of the breach, the sensitivity of the personal information involved, and the international service provided by 23andMe, the Privacy Commissioner of Canada and the UK Information Commissioner (together “the Commissioners”) decided to jointly investigate 23andMe’s privacy practices and compliance with Canada’s Personal Information Protection and Electronic Documents Act (“PIPEDA”), the UK’s General Data Protection Regulation (UK GDPR) and Data Protection Act 2018 (DPA 2018). The investigation aimed to determine:
- whether 23andMe had appropriate safeguards in place to adequately protect the personal information under its control (“Safeguards”); and
- whether 23andMe adequately notified the Office of the Privacy Commissioner of Canada (“OPC”) and the UK Information Commissioner’s Office (“ICO”) (together “the Offices”) and affected individuals about the breach (“Breach Notifications”).
23andMe was subject to a lengthy credential stuffing attack, which allowed the threat actor (the “Threat Actor”) to access and download personal information directly from thousands of customers’ accounts. In this attack, the Threat Actor used stolen login details (username or email address and password) from other websites impacted by previous breaches and then “stuffed” these credentials into 23andMe’s login page until they found matches.
Beginning on April 29, 2023, and over the course of 5 months, the Threat Actor was able to obtain access to more than eighteen thousand customers’ accounts. 23andMe stated that a total of almost 7 million customers were affected by the breach worldwide, including almost 319,000 people in Canada, and 155,600 people in the UK.
The types of personal information accessible to the Threat Actor via a customer’s account included an individual’s date of birth, sex at birth, gender, raw DNA data, health information, race and ethnicity information. Customers could also opt into a DNA Relatives (“DNAR”) feature, which allowed them to share information (such as relationship, year of birth, percentage of DNA shared with their matches, location, etc.) with genetic relatives. If this feature was activated in an account, personal information accessible to the Threat Actor could also include the personal information of thousands of other individuals to whom the owner of the credential stuffed account was genetically matched, including their name, self-reported year of birth and location (i.e., city and postal code), profile image, and race or ethnic origin. This explains why personal information relating to nearly 7 million customers was ultimately accessible to the Threat Actor, despite only 18,000 accounts being stuffed.
Safeguards
Our investigation found a number of deficiencies in 23andMe’s safeguards that contributed to the breach. Many of these deficiencies stemmed primarily from the fact that 23andMe did not take into account the risk of credential stuffing in developing its safeguards, despite the fact that credential stuffing was widely known to be a common form of attack. The deficiencies we identified generally fell under three key areas: (i) prevention; (ii) detection; and (iii) breach response:
Prevention
- No mandatory Multi-factor Authentication (MFA): MFA is a means of improving the security of authentication by requiring a user to enter more information than just a password. At the time of the breach, 23andMe made MFA optional, rather than a mandatory feature on its platform, and less than 22% of 23andMe customers had opted into either MFA or Single Sign-On (another mechanism of enhanced security at sign-on). As such, for more than three quarters of users, their password was the only control protecting access to their account, leaving them exposed to the risk of credential-based attacks. 23andMe stated that they decided not to implement MFA as they wished to avoid friction in the user experience. While we appreciate 23andMe’s expressed desire to maintain platform usability, ease of use must not come at the expense of adequate security.
- Inadequate Minimum Password Requirements: 23andMe’s password policy did not meet industry standards of best practice in place in 2023 or the ICO’s Guidance on Passwords in online services, which recommends, among other things, that passwords be no less than ten characters. 23andMe required that the password be a minimum of only eight characters, with minimal complexity requirements.
- Inadequate Compromised-Password Checks: 23andMe did not perform robust checks to verify if customers were reusing credentials that had been compromised in previous data breaches.
- No Additional Protections to Access Raw DNA Data: Once an account was accessed, there were no additional identity verification measures in place to protect the most sensitive personal information, including raw DNA data, from being accessed and downloaded from an account.
Detection
- Ineffective Detection Systems: 23andMe’s detection mechanisms failed to alert 23andMe to clear signals that a Threat Actor was attempting to gain, and had obtained, unauthorized access to large numbers of customer accounts.
- Insufficient Logging and Monitoring of Suspicious Customer Activity: 23andMe’s logging and monitoring of customers’ account activity was insufficient to detect anomalous user behaviours indicative of unauthorized access. Further, 23andMe made no device history available to customers to show them what devices had been, or were currently being used to access their account.
- Inadequate Investigation of Anomalies: 23andMe missed opportunities to identify and prevent, or at least interrupt, the attack. There were three distinct events that occurred during the period of the ongoing attack that, when viewed collectively, should have led 23andMe to detect the ongoing attack prior to October 2023. This could have, in turn, allowed 23andMe to prevent thousands of additional accounts from being subject to credential stuffing.
Breach response
- Delays in Mitigation: Despite the urgency of the situation – and 23andMe being aware of the credential-based attack, which was potentially ongoing – it took the company four days to disable all active user sessions and implement a password reset for all customers. Furthermore, it took 23andMe approximately one month to disable the self-service raw DNA download feature, and implement mandatory MFA. The absence of established protocols for responding to a credential stuffing attack may have contributed to these delays.
In light of the above, the Commissioners concluded in their Preliminary Report of Investigation (“Preliminary Report”) that 23andMe lacked appropriate safeguards commensurate to the sensitivity of information in question, and identified measures for 23andMe to implement in order to bring the company’s safeguards into compliance with our respective data protection laws. In response, 23andMe informed our Offices of a variety of information security improvements that it had implemented since the breach, many of which correspond to areas of inquiry or concern that our Offices raised during the course of the investigation. In light of the above,
- The Privacy Commissioner of Canada concludes that 23andMe contravened Principle 4.7 of Schedule 1 of PIPEDA by failing to implement appropriate safeguards to ensure the protection of the highly sensitive personal information of its customers. In light of the safeguard improvements subsequently implemented by 23andMe, the Privacy Commissioner of Canada finds this issue to be well-founded and resolved.
- The UK Information Commissioner concludes that 23andMe infringed Articles 5(1)(f) and 32(1) UK GDPR by failing to implement appropriate technical and organisational measures to ensure the integrity and confidentiality of its processing systems and services and its customers’ personal information.
Breach Notifications
Given the highly sensitive information compromised and the high probability of misuse in the context, the breach created a risk of harm to affected individuals that met the breach reporting thresholds under both PIPEDA (i.e., a real risk of significant harm or “RROSH”) and the Article 33(1)Footnote 1 and Article 34(1) UK GDPRFootnote 2, such that 23andMe was required to notify both (1) our Offices and (2) affected individuals of the breach.
Notifications to the Offices
With respect to 23andMe’s breach notifications to our Offices, the Privacy Commissioner of Canada and the UK Information Commissioner find that 23andMe’s breach reports were not made in accordance with PIPEDA and the UK GDPR, respectively, as they failed to include complete information about the personal information that was involved or likely to be involved in the breach and which was known to 23andMe when submitting its breach report, in particular raw DNA data. In respect of the timing of the breach reports, the Privacy Commissioner of Canada accepts that 23andMe provided its breach notification “as soon as feasible”. Similarly, the UK Information Commissioner considers 23andMe’s explanation for not providing its notification within 72 hours of becoming aware of the breach to be reasonable in the circumstances.
Notification to Affected Individuals
With respect to 23andMe’s breach notifications to affected individuals, the Privacy Commissioner of Canada and the UK Information Commissioner find that 23andMe’s notifications were not, in certain instances, made in accordance with PIPEDA and the UK GDPR, respectively, as they failed to provide relevant information that was known to 23andMe when submitting its notifications, including: (i) complete information about the personal information that was involved or likely to be involved in the breach; and (ii) the fact that the personal information of some individuals had been posted for sale online by the Threat Actor. In respect of the timing of the breach notifications, individuals whose accounts were directly accessed by the Threat Actor were not notified about their account having been accessed by the Threat Actor until January 2024. This was more than one month after 23andMe had completed its forensic analysis and determined which accounts had been accessed. Given this one-month delay, the Privacy Commissioner of Canada found that 23andMe did not issue notifications to individuals with stuffed accounts as soon as feasible.
In a Preliminary Report, our Offices identified measures for 23andMe to implement in order to ensure the company’s compliance with its breach notification obligations under our respective data protection laws. In response, 23andMe informed our Offices of improvements it had put in place to ensure proper breach notifications to regulators and affected individuals in future. In light of the above,
- The Privacy Commissioner of Canada concludes that 23andMe contravened section 10.1 of PIPEDA and sections 2 and 3 of the Breach of Safeguards Regulations, given the inadequacies in its breach notifications to the OPC and to affected individuals. In light of measures implemented by 23andMe subsequent to the breach, the Privacy Commissioner of Canada finds this issue to be well-founded and resolved.
- The UK Information Commissioner concludes that 23andMe failed to adhere to the requirements of Articles 33(3)(a) and (c), UK GDPR regarding 23andMe’s notifications to the ICO and failed to include all the relevant information required pursuant to Article 34(1) and (2) UK GDPR (read with Article 33(3)(c) UK GDPR) in its notifications to affected individuals.
Protection of personal information in the context of bankruptcy
On March 23, 2025, following the breach and in the face of mounting financial losses, 23andMe Holding Co. and certain of its subsidiaries, including 23andMe, filed for Chapter 11 bankruptcy under the US Bankruptcy Code. Our Offices wrote to the US Trustee overseeing 23andMe’s bankruptcy proceedings to emphasize the legal requirements for personal information relating to individuals located in Canada and the United Kingdom to be handled in compliance with our respective data protection laws. A sale approval hearing is scheduled to take place on June 17, 2025, in the US Bankruptcy Court for the Eastern District of Missouri.
If any company successfully acquires the personal information of 23andMe’s customers, our Offices will provide that company with a copy of this Report to ensure it is aware of its obligations under PIPEDA and the UK GDPR, including to protect sensitive information with robust security safeguards. Our Offices will not hesitate to take appropriate action if we consider there to be evidence of non-compliance with the applicable data privacy laws in our respective jurisdictions.
Background
- 23andMe is a multinational biotechnology company headquartered in Delaware, in the United States of America. It has been providing, and at the time of writing this report was still providing, direct-to-consumer genetic testing and ancestry services to individuals globally, including in Canada and the United Kingdom. Through an online account, customers have access to their genealogical and health-related information. Customers can access their account via the 23andMe website or via Android and iOS mobile applications (together, “the platform”).
- In order to provide its services to its customers, 23andMe collects and analyzes DNAFootnote 3 samples provided by its customers. Where consented to by the customer, their DNA sample may also be used for research purposes. Services provided by 23andMe in Canada and the United Kingdom include:
- Ancestry Service, whereby customers can access their ancestry report detailing where in the world their ancestors originate from (their “ancestry composition”). If they choose to participate, customers can share information and match with their genetic relatives through the DNAR feature. With the DNAR feature, a family tree can also be created based on the customer’s DNA Relatives matches.
- Health Service, whereby customers can access their health reports, health predisposition reports, wellness reports, and carrier status reports. Customers can also purchase additional pharmacogenetic reports, and other health-focused features and reports powered by 23andMe Research.Footnote 4
- On October 1, 2023, an individual claimed in a post on RedditFootnote 5 that they had breached 23andMe’s systems. The Reddit post offered for sale the personal informationFootnote 6 of 23andMe customers and included a sample of the stolen data.
- After a 23andMe employee discovered the Reddit post, 23andMe began an investigation and on October 5, 2023, internally confirmed that a successful credential stuffing attack had been carried out (“the breach”). On October 6, 2023, 23andMe published details of the breach on its website, including confirmation that the breach had been caused by a credential stuffing attack.Footnote 7
- A credential stuffing attack is a cyber-attack method that exploits the tendency for individuals to use the same credentials (e.g., username / email address and password combination) across multiple online accounts. The attacks are automated, often large scale, and involve the use of stolen credentials obtained from previous data breaches to unlawfully access users’ accounts on unrelated websites.
- On October 9, 2023, 23andMe disabled all active logged-in user sessions on the platform.
- On October 10, 2023, 23andMe notified all its customers of the breach via email, informing them that they would be contacted separately if it was determined that their personal information had been accessed. 23andMe required its customers to change their password and also encouraged them to enable MFA on their accounts. MFA is a multi-step account login process that requires users to enter more information than just a password. It requires proof of at least two of three factors: ‘something you know’ (e.g., password), ‘something you have’ (e.g., trusted device), and ‘something you are’ (e.g., biometric information).
- On October 15, 2023, 23andMe submitted its first of two breach reports to the ICO.
- On October 18, 2023, 23andMe submitted the first of three breach reports to the OPC, following a request by the OPC.
- In its initial October 2023 breach reports to our Offices, 23andMe reported that the personal information of 1,103,647 customers worldwide appeared to have been affected. Of these, 41,287 were individuals in Canada and 18,856 were individuals in the UK. While 23andMe advised that its investigation into the incident was ongoing, it did confirm that a “threat actor” had accessed certain 23andMe accounts through credential stuffing and downloaded the DNAR information of more than one million customers. Supplementary breach report forms submitted later in October 2023Footnote 8 indicated that 5,621,179 customers had been affected worldwide; of these, 250,082 were in Canada and 77,412 were in the UK.
- On December 4, 2023, 23andMe reported to the OPC that “uninterpreted genotype information” (raw DNA data) had also been compromised for some individuals whose account had been accessed by the Threat Actor. In that report, 23andMe also updated the numbers previously shared with the OPC, stating that a total of 6,984,430 customers had been affected by the breach worldwide, including 319,635 in Canada. In response to inquiries made by our Offices during our investigation, 23andMe stated that it unintentionally failed to submit a corresponding update to the ICO. This update was later provided to the ICO on June 24, 2024.
- In February 2024, the OPC received additional information that it had requested from 23andMe about the breach, including details about the personal information involved and the safeguards in place at the time of the breach. 23andMe also clarified that “uninterpreted genotype information,” relating to certain affected individuals, was in data files that included raw DNA data. Following the receipt of this information, the Privacy Commissioner of Canada initiated a complaint against 23andMe concerning the breach, pursuant to subsection 11(2) of Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA).Footnote 9
- Given the scale of the breach, the sensitivity of the personal information involved, and the international service provided by 23andMe, the OPC and the ICO decided to jointly investigate 23andMe’s privacy practices and compliance with applicable data protection laws. This joint investigation was publicly announced on June 10, 2024,Footnote 10 and is a demonstration of our Offices’ commitment to, and the importance of, international collaboration in responding effectively to personal data breaches.
- The joint investigation was conducted in accordance with Canada’s PIPEDA and the UK’s data protection legislation, namely the UK General Data Protection Regulation (UK GDPR) and Data Protection Act 2018 (DPA 2018). This international collaboration was made possible by the OPC and the ICO’s participation in a Memorandum of Understanding pursuant to section 23.1 of PIPEDA and Article 50 UK GDPR.
- This joint investigation aimed to determine:
- the volume and nature of personal information compromised via the breach, including the number of individuals located in Canada and in the UK whose accounts were directly accessed or may have been accessed, the type of personal information exposed as a result of such unauthorized access, including raw DNA data, and the potential harms to affected individuals;
- the appropriateness of security safeguards in place to protect customer accounts and the personal information within those accounts (including raw DNA data), the effectiveness of those safeguards at identifying unauthorized access over an extended period, and the adequacy of subsequent security enhancements; and
- the adequacy, quality, and timeliness of breach notifications to our Offices and affected individuals.
Methodology
- Our Offices analyzed submissions and other materials provided by 23andMe in response to our requests for information and during interviews with key staff at 23andMe. Our Offices also reviewed available open-source information related to the breach.
- It should be noted that our Offices did not get access to all documents requested, including certain copies of 23andMe’s internal incident logs and the forensic investigation report,Footnote 11 and were therefore unable to analyse them as part of the investigation. The company stated it could not share these on the basis of solicitor-client privilege in Canada, legal professional privilege in the UK, and the work product doctrine in the US (together “solicitor-client privilege”).Footnote 12
- After completing the evidence-gathering phase of the investigation, the Commissioners issued a Preliminary Report to 23andMe. The Preliminary Report set out the rationale for the Commissioners’ provisional findings, identified the matters of concern detailed below, and stated the Privacy Commissioner of Canada’s recommendations and the UK Information Commissioner’s provisional requirements to bring the company into compliance with PIPEDA and UK GDPR. 23andMe provided written representations in response to the preliminary findings detailed in the Preliminary Report. As part of the ICO proceedings, 23andMe provided further representations during an oral hearing that took place on April 30, 2025 (the “Oral Hearing”). We have incorporated 23andMe’s responses into this Report of Findings where appropriate.
- Throughout the investigation, our Offices experienced delays in receiving responses from 23andMe. The lack of detail in some responses also necessitated multiple rounds of clarifications. 23andMe cited staff absences, significant ongoing litigation, a reduction in workforce numbers, and extensive changes in personnel to explain the delays in providing its responses and any inconsistencies in those responses.
Analysis
Details of the Breach
- The Threat ActorFootnote 13 carried out a credential stuffing attack between April 29, 2023, and September 20, 2023, in which 18,222 customers’ accounts were accessed worldwide, including 769 in Canada and 611 in the UK.Footnote 14 Through these stuffed accounts, the Threat Actor further accessed the personal information of almost 7 million additional customers by leveraging the DNAR feature as detailed in paragraph 29. A chronology of events that occurred during the breach is detailed below.
- The Threat Actor conducted an initial period of intense credential stuffing activity from April 29, 2023, to May 16, 2023, during which 9,974 accounts were successfully accessed.
- In July 2023, the Threat Actor used a computer program to log in to a free account with no associated DNA sample over a million times throughout a single day. This was part of an unsuccessful attempt to initiate “profile transfers.” With respect to profile transfers, we note that a 23andMe account can hold one or more profiles. Once a customer registers their 23andMe test kit, a customer profile for their kit is created. A customer may choose to transfer their profile to a separate account, for instance, to authorize another user to manage it on their behalf.Footnote 15 Due to this intense volume of logins during a single day, 23andMe’s platform “crashed,” meaning that it stopped working, and 23andMe users were unable to access the platform. Later that month, the Threat Actor made further attempts to initiate profile transfers, this time involving hundreds of 23andMe customer accounts, and was once again unsuccessful.
- After discovering the attempted profile transfers, 23andMe investigated the incident and took necessary measures to prevent unauthorised profile transfers (as detailed further below in paragraph 91). The investigation that 23andMe undertook at that time did not link the incident to a wider attack against the platform.
- On August 10, 2023, 23andMe received messages (via its customer portal) from an individual claiming to have stolen the data of over 10 million of its customers, amounting to 300 terabytes of data. According to 23andMe’s incident logs, around the same time, a 23andMe employee noted that a user with the same username had made a similar claim on Reddit (as detailed further below in paragraph 94). This claim was investigated by 23andMe’s security team and categorized as a hoax.
- In September 2023, the Threat Actor carried out a second intense period of credential stuffing activity,Footnote 16 resulting in an additional 4,364 accounts being compromised.
- Through a series of attacks between April and September 2023, the Threat Actor:
- crashed the platform by attempting to access the same account over one million times in a single day;
- attempted approximately 400 unsuccessful profile transfers;
- scraped (i.e., copied via automated means) the DNAR profile information and family tree information of millions of customers linked to the stuffed accounts of customers that had opted into the DNAR feature;
- scraped the ancestry composition, and health information from thousands of stuffed accounts; and
- downloaded raw DNA data relating to a number of individuals worldwide whose accounts had been subject to credential stuffing (see further details at paragraph 31 and later in this report).
- Despite all of this activity, 23andMe did not detect that the platform was under a credential stuffing attack until October 2023. It was only when the Threat Actor advertised the stolen data for sale on Reddit on October 1, 2023, that 23andMe further investigated the incident and confirmed that a data breach had occurred.
Affected individuals and compromised personal information
- Almost 7 million 23andMe customers worldwide were affected by this breach, which represented almost half of 23andMe’s active customers at the time. The affected individuals fall into one of the following two categories: (i) individuals whose DNAR and family tree profiles were affected, and (ii) individuals whose accounts were stuffed.
- When the DNAR feature is enabled in an account, either 1,500 or 5,000 customer DNAR profiles – depending on the subscription level – are visible through that account. Therefore, by accessing 18,222 customers’ accounts, the Threat Actor was able to leverage this feature to scrape information from the DNAR profiles of almost 7 million customers.
- Information contained in DNAR Profiles: The types of personal information contained within the DNAR profiles included name,Footnote 17 self-reported year of birth and location (i.e., city and postal code), profile image, and race or ethnic origin. It could also have included information about how an individual is related to the individual associated with the stuffed account, such as a percentage of the DNA shared, matching DNA segments, IBD (i.e., identical by descent)Footnote 18 segments and other family tree information.
DNAR Profiles, Ancestry Reports and Family Tree Profiles
Number* of affected individuals reported by 23andMeType of compromised PI Canada UK Worldwide DNAR Profiles 244,583 120,031 5,497,376 Ancestry ReportsFootnote 19 245,208 120,504 5,512,131 Family Tree Profiles 74,282 35,561 1,468,791 * The DNAR Profiles and Family Tree Profiles groups are mutually exclusive, while the DNAR Profiles and Ancestry Reports are not mutually exclusive. - Information contained in stuffed accounts: The types of personal information accessible to the Threat Actor through a stuffed account – in addition to any DNAR and family tree information, as detailed in paragraph 30 above – included some or all of the following:
- full name, date of birth, sex at birth, gender, email address, country and postal code of current residence, weight and height;
- raw DNA data that provides advanced views of all uninterpreted raw genotype information, which includes data beyond what is included in the reports 23andMe provides to its customers;
- health reports that detail genetic health risks (variants associated with increased risk for certain health conditions), pharmacogenetic reports (variants that may influence the body’s ability to process some medications), carrier status reports (variants that can cause inherited conditions), and, in respect of some customers, self-reported health conditions; and
- ancestry reports that comprise information about ethnicity based on DNA, such as regions of origin, maternal and paternal haplogroups,Footnote 20 and Neanderthal ancestry.Footnote 21
- On July 16, 2024, 23andMe reported the following numbers of affected individuals for each type of compromised personal information.
Credential Stuffed Accounts
Number of affected individuals reported by 23andMeStuffed Accounts Canada UK Worldwide Total: 769 611 18,222 Type of compromised PI Canada UK Worldwide Raw DNA (downloaded) 1* 0 18* Raw DNA (accessed/browsed)Footnote 22 2 2 49 Health Reports 413 320 8,217 Self-reported Health Condition 2 3 63 * As detailed in paragraph 33 below, these numbers were amended following further analysis by 23andMe. - Our Offices identified deficiencies in 23andMe’s forensic analysis of raw DNA downloads suggesting that the Threat Actor may have downloaded raw DNA for a higher number of accounts (see paragraphs 194-195 for additional details). At the Oral Hearing on April 30, 2025, 23andMe provided updated statistics on the number of affected individuals; it established these statistics after receiving the Preliminary Report and following further analysis. 23andMe informed our Offices that through this new analysis, they found that the Threat Actor only downloaded the raw DNA data of four individuals worldwide, none of whom were located in Canada or the UK. Neither the OPC nor the ICO have independently verified these figures.
Issue 1: Did 23andMe have appropriate safeguards to adequately protect personal information under its control?
- Our Offices identified numerous deficiencies in 23andMe’s security safeguards that contributed to the Threat Actor’s ability to gain unauthorized access to the compromised personal information. The Commissioners find that, for the reasons outlined below, the safeguards that were in place at the time of the breach were not adequate or appropriate to protect the vast amount of sensitive personal information under the control of 23andMe. As a result, the Commissioners find that at the time of the breach, 23andMe did not comply with Principle 4.7 of Schedule 1 of PIPEDA and was in breach of Articles 5(1)(f) and 32(1)(b) and (d) UK GDPR, respectively.
- Principle 4.7 of Schedule 1 of PIPEDA provides that personal information shall be protected by security safeguards appropriate to the sensitivity of the information. As set out in Principle 4.7.1, “[t]he security safeguards shall protect personal information against loss or theft, as well as unauthorized access, disclosure, copying, use, or modification.”
- Principle 4.7.3 of Schedule 1 of PIPEDA provides that methods of protection should include: (a) physical measures, for example, locked filing cabinets and restricted access to offices; (b) organizational measures, for example, security clearances and limiting access on a “need-to-know”; and (c) technological measures, for example, the use of passwords and encryption.
- Article 5(1)(f) UK GDPR states that “personal data shall be processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures (‘integrity and confidentiality’).”
- Article 32(1) UK GDPR states that, “taking into account the state of the art, the costs of implementation and the nature, scope, context and purposes of processing as well as the risk of varying likelihood and severity for the rights and freedoms of natural persons, the controllerFootnote 23 and the processorFootnote 24 shall implement appropriate technical and organisational measures to ensure a level of security that is appropriate to the risk.”
Sensitivity of personal information
- Personal information that is sensitive requires a higher level of protection. The Privacy Commissioner of Canada and the UK Information Commissioner find that some of the personal information processed by 23andMe is highly sensitive personal information under PIPEDA and special category data under the UK GDPR. Therefore, 23andMe should have implemented commensurately strong security safeguards to protect this personal information.
- The OPC’s Interpretation Bulletin on Sensitive InformationFootnote 25 explains that medical information is of the utmost sensitivity and should receive the highest degree of protection.Footnote 26 The Bulletin further states that personal information that involves the collection, use and disclosure of an individual’s ethnicity is generally considered sensitive.
- The joint statement issued in 2017 by the OPC and its provincial counterparts in Alberta and British Columbia regarding Direct-to-consumer genetic testing and privacyFootnote 27 states that genetic information, when combined with contact and health information, paints a very detailed picture of an individual, and potentially their family members. As such, companies should implement strong policies and security controls to protect against the risks of unauthorized access, loss or theft, and to ensure that personal information is not further disclosed or used for purposes it was not collected for in the first place.
- Article 9(1) UK GDPR defines special category data and includes within that definition ‘personal data revealing racial or ethnic origin,’ ‘genetic data’ and ‘data concerning health.’
- The ICO’s Guidance on Special Category Data states that “the recitals to the UK GDPRFootnote 28 explain that these types of personal data merit specific protection. This is because the use of this data could create significant risks to the individual’s fundamental rights and freedoms … The presumption is that this type of data needs to be treated with greater care because collecting and using it is more likely to interfere with these fundamental rights or open someone up to discrimination.”
- The ICO’s Guidance also states that “one of the considerations for determining the appropriate level of security is the sensitivity of the personal data. You may need to consider whether you need additional security measures for your special category data.”Footnote 29
- 23andMe has been processing, and was still processing at the time of writing of this report, the personal information of millions of customers. As described above, this personal information includes ethnic and racial information, and for some customers, their raw DNA data and health information. This personal information, especially when combined with other personal information found in the DNAR profile and stuffed accounts, is considered highly sensitive.
- Therefore, our analysis focused on whether 23andMe’s safeguards were at the time of the breach – and at the time of writing of this report – appropriate given the high sensitivity of the personal information processed by 23andMe.
Credential stuffing as a risk
- To effectively evaluate and prioritize cybersecurity risks, an organization must consider both the likelihood of a threat, and the potential impact of that threat should it materialise. On that basis, 23andMe should have specifically identified credential stuffing as a high risk to its platform in terms of both likelihood and impact.
- First, credential-based attacks are the most commonly observed type of attack against web applications.Footnote 30 Multiple standards and guidelinesFootnote 31 published at the time of the breach identified credential-based attacks, including credential stuffing, as a highly likely attack method.
- Second, the nature of the highly sensitive, and potentially valuable, personal information accessible via 23andMe customer accounts made it an attractive target for malicious actors. 23andMe knew that the information found in customer accounts was highly sensitive. As such, this should have been a significant factor in 23andMe’s evaluation of the likelihood and impact of an incident and should have led the company to conclude that its customers were at an increased risk of credential-based attacks.
- Despite this, during interviews, 23andMe’s Chief Security Officer indicated to our Offices that the company had not considered credential stuffing to be a high risk to its platform. The failure to carry out an appropriate risk assessment in respect of credential stuffing influenced the design and implementation of safeguards that were in place at the time of the breach.
Safeguards at the time of the breach
- The Commissioners find that 23andMe did not properly evaluate the risk of credential stuffing attacks against its platform. Consequently, the safeguards described below were inadequate to protect the highly sensitive personal information that remains accessible within 23andMe customer accounts from credential stuffing attacks. In coming to this determination, our Offices examined three key areas: (i) prevention; (ii) detection; and (iii) breach response. These are discussed in further detail below.
Types of Authentication Methods
- In this report, we make reference to multi-factor authentication (MFA), two-stage verification (2SV), and single sign-on (SSO). However, we have used the term “MFA” where possible and unless there is a need to refer specifically to 2SV or SSO.
- Multi-factor authentication (MFA) is a means of improving the security of authentication by requiring a user to enter more information than just a password. For example, along with the password, users might be asked to enter a one-time passcode sent to their device, connect a trusted security device, or scan a fingerprint. Types of MFA that we will discuss in this report include ‘application-based’ and ‘message-based’ two-step verification.
- Application-based MFA is a method of MFA that requires the customer to install a third-party authenticator application (such as Google Authenticator) and synchronize a verification code between their account and the authenticator application. While this method of MFA places a higher technical demand on the customer, it is a more robust method than message-based 2SV, as detailed below.
- Two-step verification (2SV) is an authentication process that involves two steps. It can be email-based or SMS-based, where an email or text is sent to the customer’s registered email address, or phone number, when an attempt is made to log in to their account. This message contains a passcode which must be entered into the application for the login to be successfully authenticated. Message-based 2SV can be susceptible to interception attacks, for example, if a threat actor has also compromised the registered email address associated with an account.
- Single sign-on (SSO) provides a user with the ability to use an existing account with a trusted service provider (for example, Apple or Google) to access a different service. In this case, the trusted service provider is responsible for ensuring that the user making the request is the correct person, which it may achieve by requiring MFA or an appropriate alternative.
Safeguards at the Time of Breach
- During this investigation, we noted that at the time of the breach, 23andMe placed greater focus on safeguarding its internal and back-end infrastructure (the part of the platform that is not directly accessed by the customer).Footnote 32 For example,
- 23andMe had implemented mandatory MFA and SSO for all employee accounts accessing company information. However, for customer accounts, these features were only optional.
- While 23andMe conducted penetration testsFootnote 33 to confirm the adequacy of security for the back-end infrastructure, it never simulated credential stuffing attacks via the front-end.
- 23andMe’s incident response policies and procedures were generic and there was no specific playbook (a detailed framework for handling security incidents) for responding to a credential stuffing attack.Footnote 34
- 23andMe informed our Offices that, at the time of the breach, it had safeguards to protect against unauthorized access through its customer-facing platform (“front-end”), including:
- email address and password required for log in;
- optional application-based MFA or optional Google or Apple SSO;
- Web Application Firewall (WAF)Footnote 35 and IP address-basedFootnote 36 rules that allow the platform to,
- present a challenge (like CAPTCHAFootnote 37) to a visitor deemed suspicious,
- block access in specified circumstances that give rise to a suspicion of malicious activity, and
- rate-limit certain actions.
- a dedicated security operations team with a 24/7 on-call rotation to respond to alerts and security events;
- Security Incident and Event Management (SIEM) software that attempts to identify malicious activity and generates appropriate security alerts, for review by the security operations team; and
- a public bug bounty program that compensates individuals for reporting software errors, flaws, or faults (“bugs”) that might result in security vulnerabilities.
Prevention
- It is our view that, at the time of the breach, 23andMe’s prevention measures to protect its platform from credential stuffing attacks were inadequate in three main areas: MFA, compromised-password checks, and minimum password requirements.
Multi-factor authentication (MFA)
- Had MFA been mandatory for customer sign-in, it is very likely that the large scale credential stuffing attack, and in turn the breach, would have been prevented. In fact, research has shown that MFA is the single most effective safeguard to prevent credential-based attacks.Footnote 38 At the time of the breach, approximately 78% of 23andMe customers had not opted into either MFA or SSO, leaving them exposed to the risk of credential-based attacks, with just 0.2% of customers using the application-based MFA system offered by 23andMe, 3.2% using Apple ID’s SSO service and 18.3% using Google’s SSO service. While 23andMe told our Offices that it encouraged its customers to use MFA at the time of account creation, the vast majority did not enable this highly effective safeguard.
- The Threat Actor presented a single set of valid credentials (username and password) to the platform and this was sufficient to gain access to each stuffed account. No further safeguards were in place to verify that the legitimate account holder was entering the credentials, and as such, the platform recognized the Threat Actor as being the actual account holder. 23andMe did not alert customers of new logins to their account from an unrecognized device, IP address or location, nor of failed login attempts.
- Furthermore, there was no additional identity verification to protect sensitive information, such as raw DNA data, from being accessed and downloaded from an account.Footnote 39 A mandatory additional authentication step before high-risk actions,Footnote 40 such as downloading raw DNA data, could have prevented the Threat Actor from downloading this highly sensitive personal information.
- Making MFA optional was inconsistent with relevant standards and guidance in place in 2023,Footnote 41 which indicated that MFA should have been made mandatory to protect access to sensitive information. 23andMe explained to our Offices that it decided to make MFA optional for its customers to make the platform more user-friendly, noting that its customer base tends to be older and less likely to possess basic digital skills. 23andMe provided evidence in the form of a European Commission researchFootnote 42 report into digital skills to support this assertion. However, our Offices note that this research was conducted after the date of the breach, does not include individuals in Canada or the UK, and does not directly address the familiarity of individuals with MFA, 2SV or SSO.
- At the time of the incident, 23andMe did not offer its customers message-based 2SV as an option. Customers only had the choice between application-based MFA, SSO or relying on password alone. If 23andMe was concerned with the digital capability of its customers, it could have provided them with the option of message-based 2SV, which places less technical demands on the customer, while still significantly improving security. 23andMe now offers 2SV as the minimum requirement.
- There is strong evidence to suggest that, even before the breach occurred, 23andMe had organizational knowledge that MFA provides a significant security improvement when compared with emails and passwords alone. This evidence includes internal communications that took place between 23andMe developers prior to the breach regarding authentication best practices, as well as the actions taken by 23andMe in response to this breach. Regardless, 23andMe continued to offer MFA as an optional security feature only, for which approximately 78% of its customers chose not to enable on their accounts.
- Our Offices were provided with records of communications between 23andMe developers from August 2023, in which the implementation of potential security safeguards for a new product was discussed. The developers discussed the current state of security for 23andMe customer accounts, with particular emphasis on authentication. The most senior contributor to the discussion was the 23andMe Chief Product Officer, who stated that the group needed to address an existing “concern around users not managing their passwords well” and a need to improve security to customer accounts, in particular, for profile transfers and raw [DNA] data downloads.
- In those records, the Chief Product Officer shared their views on the ideal scenario for the new product, which would include application-based MFA before raw data download and either SMS or email-based authentication (which we understand to mean 2SV) “all the time.” To support their position, the Chief Product Officer stated that using SMS or email-based authentication was “drastically more secure than password alone” and was the current standard being used across medical and financial applications.
- When 23andMe was looking to identify compromised accounts in the immediate aftermath of the breach, it automatically discounted any accounts using MFA or Google SSO from its analysis because it was, in the company’s view, highly unlikely that those accounts could have been compromised in the breach. 23andMe subsequently informed our Offices that none of the accounts on which MFA was enabled, or where the customer used either Apple or Google’s SSO, were successfully credential stuffed.
- In its response to the breach, 23andMe subsequently implemented email-based 2SV as a mandatory minimum requirement (see paragraph 108 below). The Commissioners find that 23andMe should have identified mandatory MFA as a necessary and appropriate safeguard, and implemented it as a requirement for its customers before the breach occurred.
Compromised Password Checks
- When asked if it checked its customers’ passwords against datasets of known compromised credentials, 23andMe stated that it did not perform any such checks. However, during a subsequent interview, a 23andMe software architect stated that 23andMe checked customer passwords against a list of the 20,000 most frequently repeated passwords collected in 2021 from the “HIBP”Footnote 43 (HIBP) dataset. The Commissioners consider this to be an insufficiently robust safeguard, especially in the context where, for approximately 78% of 23andMe customers who had not implemented MFA or SSO, the password was the only control protecting access to their account.
- More robust alternatives were available to 23andMe at that time, including the potential to use third-party services to check compromised passwords or to perform an internal comparison of user passwords against a larger compromised credentials dataset. Resources to perform these checks are freely available and would have provided a significant improvement to customer security. In fact, while 23andMe had a subscription to a security service that included a feature that could check submitted credentials against the 847 million compromised passwords included in the HIBP dataset, 23andMe did not enable that feature. When asked why this feature had not been enabled, 23andMe stated that it was not viable because of the structure of the 23andMe website, but provided no further details to substantiate this claim.
- If 23andMe had checked its customers’ credentials against a larger dataset, it would have found that many of its customers were reusing credentials that had been compromised in previous data breaches. It is worth noting that 23andMe did such a check during its breach response, when trying to understand how many of the credential accounts’ passwords had been previously leaked. A more robust and systemic check against compromised passwords as a preventive measure prior to the breach would have enabled 23andMe to alert its customers, require them to use a unique and secure password and to significantly mitigate the risk of those accounts being stuffed.
Minimum Password Requirements
- Finally, we note that at the time of the breach, 23andMe’s password policy did not meet industry standards of best practice in place in 2023Footnote 44 or the ICO’s Guidance on Passwords in online services, which recommends that passwords be no less than ten characters.Footnote 45 23andMe required that the password be a minimum of only eight characters, with minimal complexity checks.Footnote 46
- Furthermore, up until August 2023, 23andMe did not prevent previous passwords from being reused when a customer reset their password, meaning that an unsecured password could be reused by the same customer.
Detection
- Our Offices recognize that any organization, even with the best protections in place, is at risk of a cyber attack. Therefore, it is important for organizations to have appropriate measures in place to detect privacy breaches early on, before they escalate.
- The Commissioners’ view is that: (i) at the time of the breach, 23andMe’s detection measures were inadequate to protect its platform from ongoing credential stuffing attacks; and (ii) when 23andMe did identify anomalies, it did not appropriately investigate these anomalies such that it failed to prevent the breach from escalating.
Inadequate detection measures
- The Commissioners find that 23andMe’s detection measures were inadequate in three main areas: (i) detection systems, (ii) digital fingerprinting,Footnote 47 and (iii) device history.
Detection systems
- There is no evidence that 23andMe’s detection mechanisms responded to clear signals that the Threat Actor was attempting to gain, and had obtained, unauthorized access to customer accounts from April through October 2023. In fact, 23andMe did not discover the breach until the Threat Actor went public in October 2023. In our view, the breach was not the result of a sophisticated attack and could have been detected by adequate detection measures.
- More specifically, despite persistent access to thousands of stuffed accounts over a five-month period, the breach was not detected and no alerts were generated. 23andMe’s failure to configure its detection mechanisms in a way that was capable of detecting an ongoing credential stuffing attack was, in part, because it had not simulated this type of attack, and had not properly considered what an ongoing credential stuffing attack would look like. While 23andMe had in place tools with the capability to detect the attack against the platform, the credential stuffing attack remained undetected because these tools had not been appropriately configured.
- We note that a key indicator of credential stuffing attacks is a distortion in the ratio of successful to unsuccessful login attempts.Footnote 48 This ratio should be reasonably consistent – subject to occasional small amounts of variance – with the average to be expected in the normal course of business. However, a credential stuffing attack, during which a threat actor submits a high volume of failed authentication attempts, will distort the ratio.
- Our Offices examined the number of daily successful and failed logins to the 23andMe platform over the period of the breach and we were able to identify two distinct periods of intense credential stuffing activity, in May and September 2023, when the ratio dropped materially (See Figure 1). This was consistent with information about the pattern of events that 23andMe provided to our Offices in response to our inquiries. These ratio distortions were a signal that 23andMe could have used to detect the ongoing credential stuffing attack. However, 23andMe did not have measures in place to detect these distortions at the time that they occurred and did not learn of this information until its internal investigation in response to the Reddit post in October 2023.
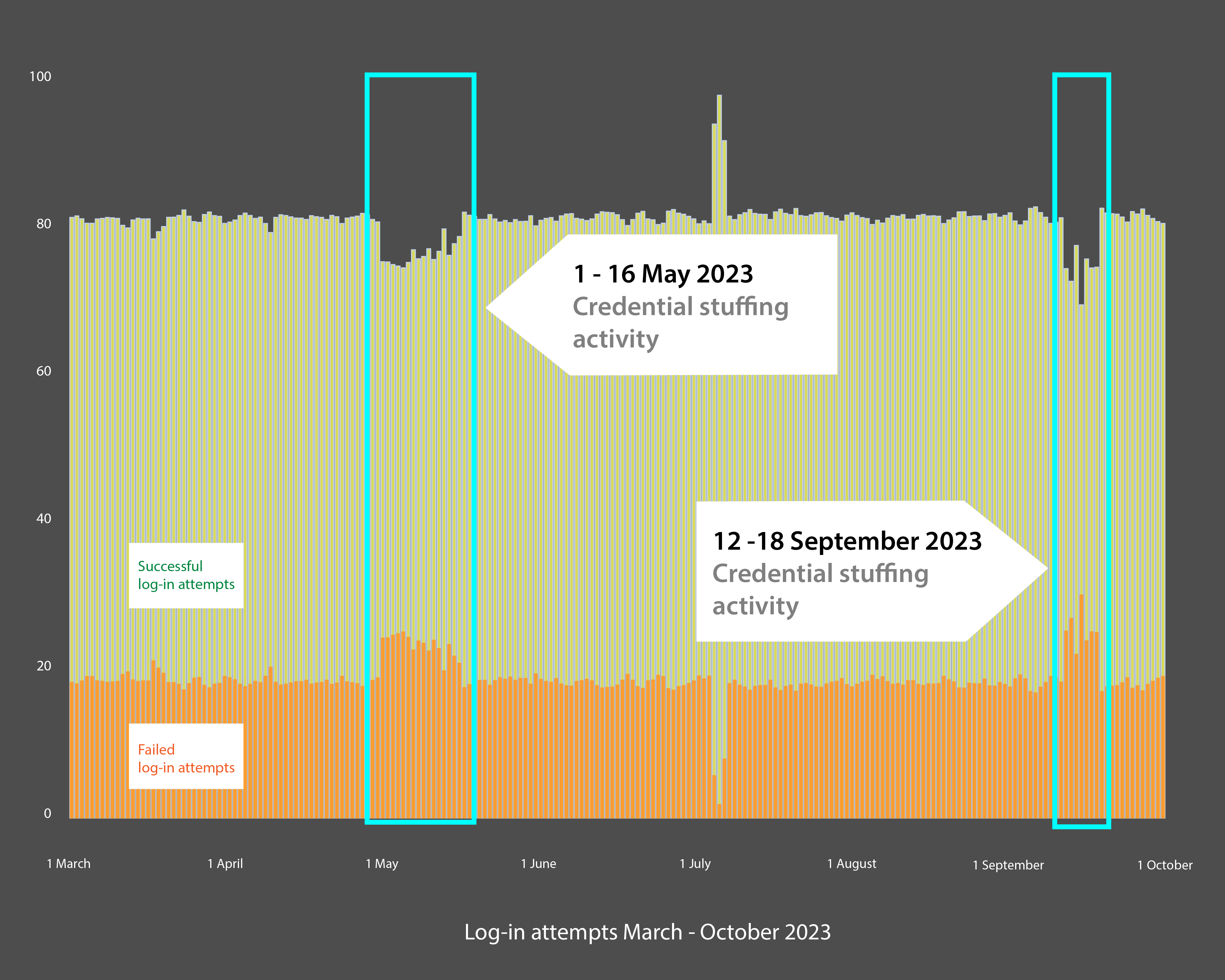
Text version of Figure 1
Our Offices examined the number of daily successful and failed logins to the 23andMe platform over the period of the breach. We were able to identify two distinct periods of intense credential stuffing activity: May and September 2023, where the ratio dropped significantly (See Figure 1). This was consistent with information provided by 23andMe to our Offices. This data indicates that 23andMe could have used the sudden fluctuations to signal the ongoing credential stuffing attack.
- Finally, it is our Offices’ understanding that at the time of the breach, 23andMe relied on a largely manual process to set the thresholds that determine what activity will generate a security alert. While this does not appear to have contributed to the breach directly, we note that reliance on a purely manual system can limit an organization’s ability to adapt quickly to evolving attack patterns or unusual activity. This approach may also result in thresholds being too rigid or outdated, increasing the risk of missed alerts or generating false alarms.
Digital fingerprinting
- Fingerprinting is the process of using information gathered from a device, browser, and network connection to build a digital fingerprint of a specific individual. The fingerprint associated with the account owner can be compared against that of the individual who is attempting to access the account. If the fingerprints do not appear to match, then an appropriate action can take place. This action could take the form of a challenge to the user, or a notification to a trusted device, which would in turn alert the genuine account owner of potential suspicious activity so that they can take measures to protect their account.
- 23andMe has in its possession the information that is required to conduct fingerprinting when customers connect to the platform. However, 23andMe did not use this information at the time of the breach to conduct fingerprinting or to detect anomalous behaviours indicative of unauthorized access to a customer account.
- If fingerprinting had been in place at the time of the breach, it could have resulted in notifications alerting 23andMe and/or the genuine account owners of potentially suspicious access, or attempted access, to the accounts (e.g., from a new device, browser or IP address). This would have provided the customer with the opportunity to take steps to protect their personal information and could also have alerted 23andMe to an increase in suspicious login attempts or logins.
- 23andMe explained that the decision not to conduct fingerprinting was made in light of its other security measures and customer privacy concerns. While our Offices appreciate the importance of customer privacy, we note that this position was not consistent with 23andMe’s privacy statement which, at the time of the breach, stated that it collected the data required to conduct fingerprinting, and that it would use personal information for the purposes of enhancing the safety, integrity and security of its services, including for the prevention of fraud and other unauthorized or illegal activities on its services.Footnote 49
Device History
- Finally, we also note that no device history was made available to customers to show them what devices had been, or were currently being, used to access their 23andMe account. If 23andMe had made this history available to customers, the customers would have had the opportunity to identify suspicious access to their accounts.
Anomalies Were Not Appropriately Investigated
- 23andMe missed opportunities to identify and prevent the attack, or at least interrupt it. There are three distinct events that occurred during the period of the ongoing attack that, when viewed collectively, should have led 23andMe to detect it prior to October 2023. This would have prevented thousands of additional accounts from being subject to credential stuffing.
The July Platform Crash
- After reviewing logs of 23andMe’s customer account logins, our Offices discovered an anomalous increase in login attempts on July 6, 2023 (See Figure 2). 23andMe explained that there had been over a million successful logins to the same customer account throughout a single day and this activity temporarily crashed 23andMe’s platform. 23andMe ultimately determined that this was part of an unsuccessful attempt to leverage the “Profile Transfer” feature.Footnote 50
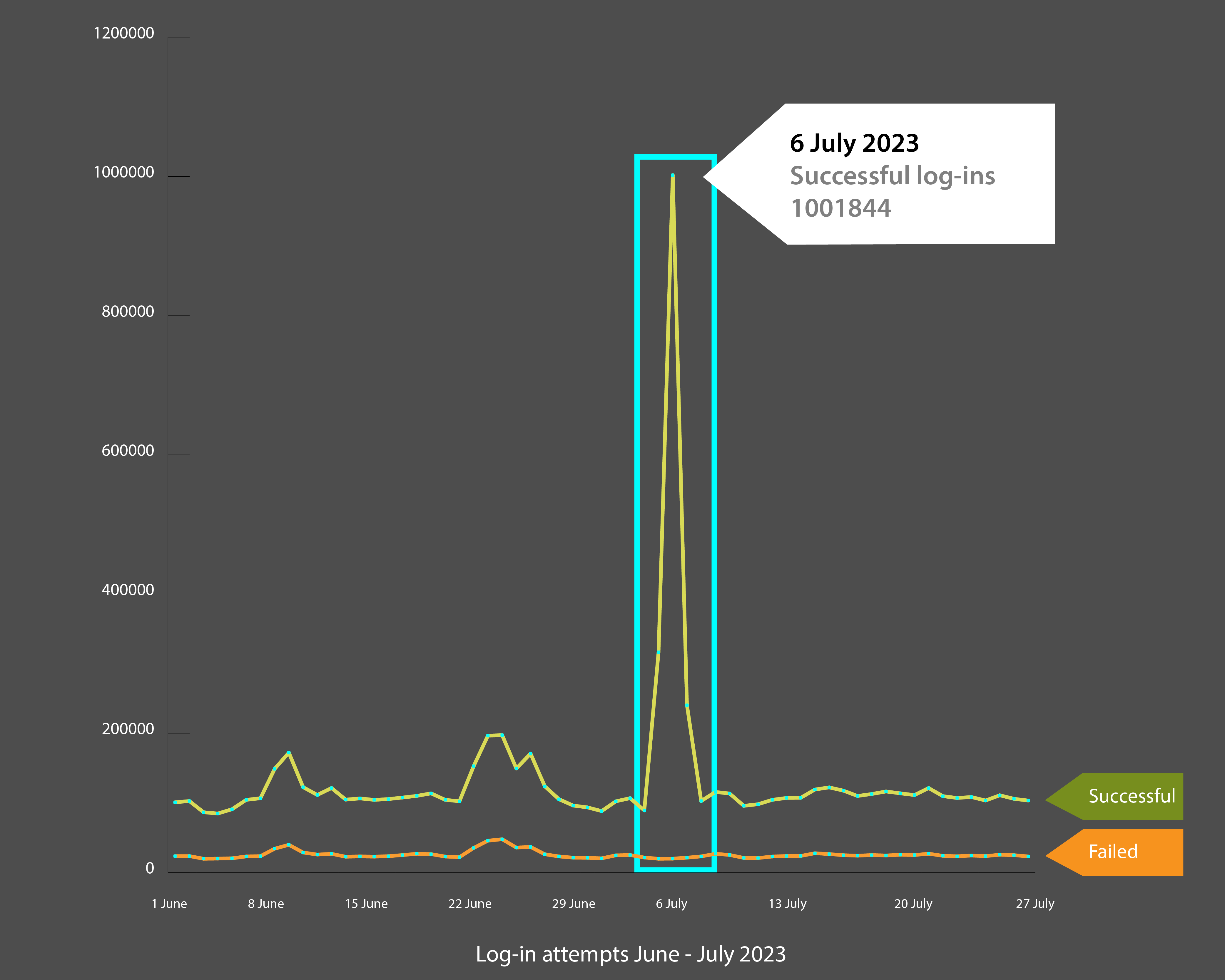
Text version of Figure 2
After reviewing logs of 23andMe’s customer account logins, our Offices discovered an unusual increase in login attempts on July 6, 2023 (See Figure 2). 23andMe explained that there were over a million successful logins to the same customer account throughout a single day. This activity temporarily crashed 23andMe’s platform. 23andMe ultimately determined that this was part of an unsuccessful attempt to leverage the “Profile Transfer” feature.
Attempted profile transfers from 400 accounts
- From July 28 to 30, 2023, there were multiple attempts by the Threat Actor to automate profile transfers, involving approximately 400 different accounts.
- This is an abnormal number of attempted profile transfers in a short period of time. Based on this abnormal activity, and noting that a user must be logged into the account associated to a profile to initiate a transfer of that profile,Footnote 51 23andMe should have recognised that unauthorized access to hundreds of accounts was occurring, indicating a potential credential stuffing attack. In response to this incident, 23andMe disabled all profile transfer requests, placed a temporary lock on potentially affected accounts, and initiated a mandatory password reset for the 400 customers. In addition, it added a system alert for its monitoring solutionFootnote 52 to capture an abnormal number of profile transfer requests. 23andMe also undertook an internal investigation, which determined that within the accounts of nineteen (19) customers in the US, limited information had been accessed.
- Through this incident, 23andMe did discover that it was possible for a customer to reset their account password to any previously used password.Footnote 53 In August 2023, 23andMe therefore made changes to prevent password re-use. However, its investigation into this July incident did not discover the ongoing credential stuffing attack.
The August 10, 2023 Claim by the Threat Actor
- As described earlier in this report, in August 2023, 23andMe received a series of messages through its customer contact portal from an individual using the pseudonym ‘bionhack,’ claiming to have breached 23andMe’s security and gathered over 300 terabytes of data relating to 10 million customers. The individual asserted that the stolen data included ancestry composition, health data, and raw DNA data.
- According to an incident log created by 23andMe’s Cyber Incident Response Team, during the same time period, a user with the same username made a similar claim on Reddit, seemingly including evidence of the alleged data breach. While the Reddit post was deleted by the time 23andMe was made aware of it, the 23andMe employee who had found the post noted that comments on the post suggested that the poster provided evidence of the data breach. A comment on the Reddit post also included an annotated image of the genetic profile of two individuals, a senior executive at 23andMe and their former spouse, claiming this to be evidence of the data breach. Another comment on the post stated that the breached data was for sale on a hacker platform.
- The incident response log was closed after 4 days, having been graded as the lowest priority level available. While 23andMe looked into the matter to assess whether the two individuals’ accounts had been accessed directly without permission, it determined within the first two days of its investigation that this was not the case. 23andMe explained to our Offices that samples of the genetic background information of both individuals could have been obtained legitimately via the DNAR feature inside the platform and noted that the senior executive in question had published their own genetic ancestry information to all 23andMe customers via a public report. 23andMe advised that it considered this, alongside the absence of any evidence that 300 terabytes of data was extracted, to be sufficient evidence to consider the claims in the Reddit post to be a hoax.
- In August 2023, 23andMe did not take steps to access or obtain the allegedly stolen data, despite the comments indicating that it was for sale on the dark web, as well as a statement by a member of the 23andMe Cyber Incident Response team that the data was probably for sale on an invite-only marketplace.
- In contrast, we note that in October 2023, 23andMe hired a third party to obtain a sample of the stolen data, and this external resource was able to verify that the breach claim was genuine. If 23andMe had similarly investigated the matter when it received the customer contact portal messages in August 2023, this may have allowed it to determine the scale of the incident, which in turn could have enabled 23andMe to implement appropriate protective measures and could have ultimately given 23andMe the opportunity to prevent the credential stuffing of almost 5,000 additional accounts in September 2023.
- 23andMe confirmed that it rarely received claims of data breaches from individuals. Considering that this was out of the ordinary, and in the context of the two other incidents in July, the Commissioners find that 23andMe should have conducted a more thorough investigation into this alleged breach.
Breach response
- Once a breach has been detected, organizations should immediately attempt to contain the breach, and implement measures to avoid additional unauthorized access to personal information.
- For the reasons explained below, the Commissioners find that 23andMe did not take remedial actions in a timely manner once it confirmed the legitimacy of the breach in October 2023.
- On October 1, 2023, 23andMe discovered the Reddit post referring to the breach. On October 5, 2023, it confirmed that the post was genuine and commenced an internal investigation into the breach. On October 6, 2023, 23andMe announced in a blog that customer profiles had been accessed without authority. Thereafter, 23andMe took the following actions as part of its breach response:
- October 9, 2023 – Four days after confirming the breach was genuine, 23andMe disabled all active logged-in user sessions,
- October 10, 2023 – 23andMe emailed all customers, informing them of the breach and mandating a password reset. Customers were also encouraged to enable MFA on their accounts;
- November 2, 2023 – 23andMe disabled the self-service raw DNA data download feature. Customers were required to contact the 23andMe Customer Care team directly to request a raw DNA data download. The feature was re-enabled on February 27, 2024, with an additional verification step that required customers to provide their date of birth; and
- November 9, 2023 – 23andMe made email-based 2-step verification (2SV) mandatory for all new customers and existing customers who had not already enabled application-based MFA or SSO.
- We also note that 23andMe offered dark web monitoringFootnote 54 to certain individuals where it deemed it appropriate, depending on the customer’s specific situation and the type of personal information compromised.
Delay in disabling active user sessions and implementing password reset
- The 23andMe Incident Response Procedure classifies breaches involving lost customer data as the highest priority level and indicates that such breaches necessitate an immediate fix. The Commissioners note that despite the urgency of the situation – and 23andMe being aware of the credential-based attack, which was potentially ongoing – it took the company four days to disable all active user sessions and implement a password reset for all customers.Footnote 55
Delay in Disabling the Self-Service Raw DNA Download Feature
- Despite the eventual global password reset, the residual risk of continued unauthorized access to user accounts remained, including the risk of unauthorized raw DNA downloads. For example, if a customer used the same credentials for their 23andMe account as they did for their email account, the Threat Actor could have accessed emails about the password reset and maintained its access to the 23andMe account. Therefore, 23andMe should have, with greater urgency, implemented further measures to protect the highly sensitive data in those accounts.
- It took 23andMe almost one month to disable the self-service raw DNA data download feature. 23andMe ought to have known that DNA was at risk of being downloaded by the Threat Actor as soon as it identified that credential stuffing was the source of the attack, as this meant that the Threat Actor would have unrestricted access to the raw DNA download feature within the stuffed accounts. While our Offices have no evidence to suggest that any suspicious raw DNA downloads took place after the global password reset on October 10, 2023, given the high sensitivity of DNA information, disabling this feature or implementing a second layer of protection to prevent any further unauthorized downloads by the Threat Actor should have been an immediate priority.
- When 23andMe re-enabled the raw DNA download feature in February 2024, it implemented an additional verification measure, such that customers who have already logged into their accounts using MFA are now required to also provide their date of birth to use this specific feature. The Commissioners note that there are industry concerns regarding the use of dates of birth as a method of verification because such information may be available through various other means, including public posts on social media, or through previous data breaches.Footnote 56 However, the Commissioners have considered the appropriateness of this new measure in the context of the other improvements 23andMe has made since the breach.
Delay in Implementing Mandatory MFA
- The only form of MFA that 23andMe had available for immediate implementation at the time that it realized that the credential stuffing attack was legitimate was application-based MFA. This feature was already offered as an option to its customers.
- As explained in paragraph 54 above, this method of MFA requires the customer to install a third party authenticator application (such as Google Authenticator) and to synchronize a verification code between their 23andMe account and the authenticator application. This form of MFA places a higher technical demand on the customer when compared to 2SV. While 23andMe had the option of making application-based MFA mandatory immediately, it instead chose to develop an email-based 2SV solution, which took the company over one month to complete.
- Therefore, during the month it took to develop the email-based 2SV, 23andMe accounts and the sensitive information they contain remained vulnerable to further credential stuffing attacks, although a stronger application-based MFA was already available. While we appreciate 23andMe’s desire to maintain platform usability, ease of use must not come at the expense of adequate security.
- In conclusion, by delaying the implementation of the protective measures detailed above, 23andMe left its systems and its customers’ personal information vulnerable to unauthorized access longer than necessary. We note that the absence of incident-specific playbooks (i.e., in this instance, a set of established protocols for responding to a credential stuffing attack) to instruct 23andMe incident responders on priority actions may have contributed to the delay in implementing some necessary and appropriate protective measures, such as resetting passwords and disabling raw DNA access.
Conclusion on Issue 1
- Given all of the above, when considered together, the Commissioners find that 23andMe did not implement safeguards appropriate to the highly sensitive information entrusted to it by its customers. As detailed further above, the Commissioners were particularly concerned by 23andMe’s failure to:
- properly consider the risk of credential-based attacks in the design of its information security framework;
- implement adequate measures to protect against credential stuffing attacks, such as MFA, as well as appropriately calibrated tools to detect and flag suspicious activity indicative of a credential stuffing attack; and
- properly investigate events that would indicate the risk of a breach, such as the Threat Actor’s breach claims in August 2023, to prevent the breach from escalating.
- OPC: In view of the above, the Privacy Commissioner of Canada concludes that the safeguards implemented by 23andMe were not adequate or appropriate to protect the vast amount of sensitive personal information under its control, which resulted in 23andMe failing to comply with Principle 4.7 of Schedule 1 of PIPEDA.
- ICO: In view of the above, the UK Information Commissioner concludes that 23andMe breached Articles 5(1)(f), 32(1)(b) and 32(1)(d) UK GDPR by failing to implement appropriate safeguards to ensure the integrity and confidentiality of both its processing systems and services and its customers’ personal information.
Assessment of 23andMe’s current safeguards
- Given the contraventions identified above, our Offices identified measures for 23andMe, to implement in order to bring its safeguards into compliance with section 4.7 of Schedule 1 of PIPEDA and its processing into compliance with Articles 5(1)(f) and 32(1) UK GDPR respectively. In determining these measures, our Offices considered requirements under the law, the usability of the services for 23andMe’s customers, and alignment with recognized standards, to ensure that the personal information that 23andMe is responsible for protecting is appropriately secured.
- In the Preliminary Report, the Privacy Commissioner of Canada issued detailed recommendations, and the UK Information Commissioner’s issued detailed provisional requirements to 23andMe, which are summarized below:
- upgrade the current solution for screening passwords to enable effective detection of compromised passwords;
- implement a password policy which provides an appropriate level of security to its customers’ personal information in light of the risks posed by its processing activities, taking into account the findings of the Preliminary Report;
- enhance its measures in place to protect access to raw DNA data;
- enhance its logging and monitoring of customer activity and the detection of indicators of potentially unauthorised activity within customer accounts;
- perform regular attack simulations and exercises against the platform based upon the most likely attack methodologies;
- review and amend, as appropriate, organizational and governance measures, to ensure the ongoing assessment and regular review of 23andMe’s information security program, including its information security controls and incident response capabilities; and
- review, on an ongoing basis, its security safeguards, taking into account evolving security standards and industry best practices.
- In response to the Preliminary Report, 23andMe informed our Offices of the new security measures that it had implemented by December 31, 2024. Many of these measures addressed specific lines of questioning and areas of concern identified by our Offices during the course of the investigation. The Commissioners consider, on balance, that these satisfy the recommendations made by the Privacy Commissioner of Canada and the provisional requirements communicated by the UK Information Commissioner in the Preliminary Report. These measures included:
Passwords
- increasing the minimum password length to 12 characters, preventing customers from repeating any of their previous five passwords, reminding customers to use a unique password, and preventing customers from using repeated characters or contextual strings in their passwords;
- checking customer passwords against the entire “HIBP” database of almost 1 billion compromised credentials (updated on a monthly basis) when customers register, sign-in and reset their passwords;
MFA
- implementing mandatory email-based two-factor authentication MFA for customers when logging on to the platform (whilst also permitting customers to continue to use SSO services offered by Apple and Google);
Enhanced protection for sensitive data
- requiring customers to provide the date of birth associated with their account in order to download raw DNA data, health data or to complete a profile transfer;Footnote 57
- adding a 48-hour delay between a raw DNA data download request being made and the email being sent to notify the customer that the request has been actioned;
Penetration testing
- conducting tests simulating credential stuffing attacks using generated accounts;
- carried out five cyber security exercises by the end of 23andMe’s 2025 financial year (March 31, 2025);
Monitoring and Detection
- updating rules for monitoring and tools to detect abuse by potential threat actors, including to detect and generate alerts for incidents of credential stuffing and password spraying;Footnote 58
- introducing over 253 new security information and event management detection alerts, which it continually adjusts based on traffic activity and indication of attack;
- deploying a solutionFootnote 59 that carries out risk-based monitoring beyond user sign-in, including in relation to user behaviour on the platform;
- engaging a third-party to monitor and report on any dark-web posts relating to 23andMe;
- Increasing the coverage of its monitoring, detection and response tools including its Web Application Firewall and Threat Intel Reports;
- implementing a trusted browser functionality which allows customers to register a “trusted device” (used to access their 23andMe account) for a period of 400 days, and also offers an “Account Event History” report. Customers can download the report which displays every login, attempted login and download with the associated IP address and approximate location (based on the IP address);Footnote 60
- reconfiguring internal logs to allow the 23andMe Security Team to better track and identify malicious activities;
Organizational measures
- improving 23andMe’s organizational structure related to security, including creating a closer working partnership between 23andMe’s security, engineering and product teams; and
- updating security processes and procedures including its Cyber Incident Response Procedure, Privacy and Security Incident Response Policy and Privacy Incident Response and Tracking Procedure.
- Taken collectively, the Commissioners accept that the additional safeguards implemented by 23andMe are sufficient to resolve the safeguard concerns identified by the investigation. In light of the measures that 23andMe has implemented since the breach:
- the Privacy Commissioner of Canada finds the Safeguards aspect of the matter, and specifically contraventions of Principle 4.7 of Schedule 1 of PIPEDA, to be resolved; and
- the UK Information Commissioner finds that, as of 31 December 2024, 23andMe has implemented appropriate technical and organisational measures to ensure a level of security for its customers’ personal information which is appropriate in light of the risks posed by the processing it performs, as required by Articles 5(1)(f) and 32(1) UK GDPR.
Issue 2: Did 23andMe adequately notify our Offices and affected individuals about the breach?
- For the reasons explained below:
- the Privacy Commissioner of Canada finds that 23andMe contravened section 10.1 of PIPEDA, and sections 2 and 3 of the Breach of Safeguards RegulationsFootnote 61 (“PIPEDA Breach Regulations”); and
- the UK Information Commissioner finds that 23andMe failed to comply with the requirements of Article 33 UK GDPR in a manner that aggravated the alleged infringements of Article 5(1)(f), Article 32(1)(b) and Article 32(1)(d) UK GDPR set out above and additionally failed to comply with Article 34 UK GDPR, although following oral and written representations, this was not deemed to be an aggravating factor.
- As detailed below, the Commissioners identified deficiencies with the content of 23andMe’s breach notifications to our Offices and the information provided to affected individuals. In addition, the Privacy Commissioner of Canada identified issues with the timing of the notifications to affected individuals in Canada whose accounts were directly accessed by the Threat Actor.
OPC notification requirements
- Section 10.1 of PIPEDA provides that organizations that experience a breach of security safeguards involving personal information must report the breach to the OPC if it is reasonable to believe in the circumstances that the breach creates a real risk of significant harm to affected individuals.
- Additionally, subsection 10.1(3) of PIPEDA states that the organization must notify any affected individual of the breach, unless otherwise prohibited by law, to allow these individuals to take steps, if any are possible, to reduce or mitigate the risk of harm that could result from the breach.
- In both cases, the notifications need to contain the information prescribed in sections 2 and 3 of the PIPEDA Breach Regulations and be done as soon as feasible after the organization determines that the breach has occurred.
ICO notification requirements
- Article 33(1) UK GDPR provides that, “in the case of a personal data breach, the controller shall, without undue delay and where feasible, not later than 72 hours after having become aware of it, notify the Commissioner, unless the personal data breach is unlikely to result in a risk to the rights and freedoms of persons. Where the notification is not made within 72 hours, it shall be accompanied by reasons for the delay.”
- Article 34(1) UK GDPR provides that “when the personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the controller shall communicate the personal data breach to the affected data subjects without undue delay.”
Did the breach create a risk of harm to affected individuals?
- An organization’s breach reporting obligations under PIPEDA and the UK GDPR are triggered when a certain threshold of risk to the affected individual(s) is met. For the OPC, this threshold is met when the breach creates a “real risk of significant harm” to the individual.Footnote 62 For the ICO, the threshold to notify the UK Information Commissioner is met when the breach creates “a risk to the rights and freedoms of natural persons,”Footnote 63 while the threshold for notifying individuals is met when the breach creates a “high risk to the rights and freedoms of natural persons.”Footnote 64 For the purpose of this report, we will refer to these thresholds collectively as “the risk of harm thresholds” (or the “thresholds”). This is not to say, however, that the respective thresholds are the same.
- For the reasons explained below, our Offices are of the view that the breach created a risk of harm to affected individuals that met the thresholds under both PIPEDA and the UK GDPR, such that 23andMe was required to notify our Offices and affected individuals of the breach.
- 23andMe did notify our Offices and affected individuals about the breach. However, when our Offices sought information from 23andMe about its ‘risk of harm assessment,’ 23andMe took the position that the breach did not create a risk of harm to individuals that met the thresholds under PIPEDA and the UK GDPR. The Commissioners are concerned that 23andMe’s inadequate assessment of both the risk of harm to individuals and the full impact of the breach may have led to the inadequacies in its notifications that are described in detail below. We also note that at the time of the breach, 23andMe did not have a framework in place to guide its risk of harm assessment, which may have further contributed to the gaps we identify below.
- Paragraphs 135 to 154 below explain how this breach created a risk of harm to individuals that met the reporting thresholds under both PIPEDA and the UK GDPR. The following sections set out the deficiencies identified in 23andMe’s risk of harm assessment, and examine the potential risks of harm that our Offices consider to have resulted from the breach.
23andMe’s Assessment of the Risk of Harm
- In response to our Offices’ request for information about its risk of harm assessment, 23andMe stated that for individuals whose raw DNA and/or health information was compromised (individuals with stuffed accounts), the most severe potential outcome would be discrimination or reputational damage if that information became public. However, 23andMe asserted that it is highly improbable that this harm would occur because: (i) the affected individuals’ health reports and raw DNA data were not made available on the dark web; and (ii) even if the Threat Actor had decided to make such information available on the dark web, it would not seem probable (and would likely be illegal) that insurance companies or employers would search the dark web for such information to assist them in making decisions about those affected individuals.
- 23andMe felt it was highly improbable that harm could happen. However, it acknowledged that an individual whose account has been stuffed could suffer negative outcomes if that information became public – which is also our view. Indeed, it is possible (even if not legal) that this information could be used by an insurance company or employer to assist in their decision-making regarding the individual, which could in turn result in adverse treatment, such as the loss of employment opportunities or denial of health insurance coverage. These harms could be particularly serious for individuals who are predisposed to a serious medical condition.
- We do not, however, accept that such harms are highly improbable. In coming to this determination, we note the following:
- First, there is no certainty that individuals’ raw DNA data and health information were not sold or advertised on the dark web. 23andMe’s position that this data was never sold on the dark web seems to rely on the result of dark web searching by a third-party threat intelligence service provider and assurances provided by the Threat Actor. In fact, in its August 2023 posts, the Threat Actor indicated that it had sold data from the breach (including raw DNA) to a businessman in the Middle East.Footnote 65
- Secondly, even if the raw DNA and health information from stuffed accounts have, to this day, not been made available on the dark web, as 23andMe indicated, this does not eliminate the risk that the information may be posted on the dark web in the future as it is not uncommon for threat actors to wait some time before posting stolen data after a breach. In this regard, we note that 23andMe offered dark web monitoring to certain affected individuals so that these individuals could receive alerts if their personal information were to be discovered on the dark web. In addition to the possibility of being posted on the dark web, the information could be sold directly to other entities. Individuals whose personal information is sold could face extortion or blackmail, such as by a malicious actor demanding payment in exchange for not releasing their highly sensitive information.
- Furthermore, while the use of genetic information by employers or insurance companies to make adverse decisions about individuals would generally be illegal under Canadian and UK law,Footnote 66 this does not completely eliminate the associated risk.
- 23andMe also stated that individuals whose DNAR profile was compromised could suffer anxiety or embarrassment if that information became public. However, 23andMe asserted that this harm is also unlikely to occur, as these individuals had already consented to share this information with thousands of other 23andMe customers. 23andMe further asserted that individuals who would be likely to experience anxiety or embarrassment or be harmed in some way as a result of this information being made public would not have shared the information with thousands of individuals via the DNAR feature. 23andMe added that by “agreeing to participate and willingly share ancestry information with complete strangers, claims of anxiety and fear of harm seem disingenuous, especially where a customer’s physical address was not part of the information disclosed.”
- The Commissioners disagree with 23andMe’s assessment and find that the social nature of the DNAR feature does not negate or diminish the risk of harm to individuals who share their information via that feature. More specifically:
- Customers who chose to share their data with 23andMe account holders with a shared interest in learning about their health and ancestry would not have envisioned or consented to that information being accessed by a Threat Actor with malicious motives, or that it would be publicly exposed on the internet.
- Customers can deactivate the DNAR feature and stop sharing information at any time. In contrast, individuals affected by the breach lost the ability to control their personal information once it was in the hands of the Threat Actor.
- Finally, 23andMe states that it is unaware of any affected individual suffering actual harm as a result of the breach. While this is a relevant factor to consider, it is not conclusive in itself. Even if harm has not materialized for any affected individual, it does not mean that there is no risk of harm. Indeed, the ICO received several complaints against 23andMe, and some of the complainants described feeling extremely anxious about what the breach could mean for their personal, financial and family safety in the future and expressed concern about the perceived ability to target a specific group using their DNA.
Our Offices’ assessment of the risk of harm
- Subsection 10.1(8) of PIPEDA states that the following factors are relevant to determining whether a breach of security safeguards creates a real risk of significant harm to the individual: (a) the sensitivity of the personal information involved in the breach; (b) the probability that the personal information has been, is being or will be misused; and (c) any other prescribed factor.Footnote 67
- According to ICO’s Guidance on Personal Data Breaches,Footnote 68 organisations should assess the potential adverse consequences for individuals’ rights and freedoms. This involves an assessment of both the severity of the potential or actual adverse impacts on individuals as a result of a breach, and how likely they are to happen.
Sensitivity of the Personal Information
- As detailed in paragraph 39 above, the personal information involved in the breach is considered to be highly sensitive by the OPC and constitutes special category data according to the ICO. For individuals that had their DNAR profile impacted, this included information about their ethnic and racial origin. For individuals that had their account stuffed, this included information about their ethnic and racial origin, but also their health and genetic information (raw DNA data).
Probability of Misuse
- As detailed in the paragraphs that follow, the Commissioners consider that there remains a high probability of this information being misused. In arriving at this conclusion, the Commissioners considered the following circumstances as increasing the probability of misuse:
- the personal information was accessed by a Threat Actor who demonstrated a malicious intent to harm individuals;
- a large amount of personal information was obtained by the Threat Actor;
- the personal information was in unencrypted formFootnote 69; and
- the personal information has not been recovered, and certain information (DNAR profile information) was offered for sale online on at least two occasions.
Demonstrated malicious intent
- First, the highly sensitive personal information was accessed by the Threat Actor who actively exfiltrated it over several months and attempted to profit from that personal information by posting the stolen data, including raw DNA data, for sale on at least two websites (BreachForumsFootnote 70 and HydraMarketFootnote 71) that were frequented by individuals with nefarious intent. These websites have since been shut down.
- In a post advertising the breached data, the Threat Actor grouped the data by ethnic origin and nationality with specific reference to individuals with Ashkenazi Jewish and Chinese ancestry. The grouping of the customer data by ethnic origin and nationality suggests that the Threat Actor may have been motivated by a desire to cause harm to these specific groups or to make the information available to other actors who wished to do so. In its posts, the Threat Actor also referenced the escalating conflict in the Middle East, which could indicate that its intent to cause harm to individuals of a certain nationality or ethnic origin was, at least partially, motivated by the tense geopolitical environment of that period.Footnote 72 However, 23andMe told our Offices that it did not verify whether the Threat Actor groupings were accurate or try to categorize affected individuals by ethnic origin for the purposes of its risk assessment.
High Volume of Personal Information
- Secondly, many distinct pieces of personal information were breached for millions of individuals, which could increase the value of that information. This could attract more malicious actors to obtain the information, increasing the likelihood that it could be misused.
Personal Information Was Unencrypted
- Thirdly, we understand that the information for both DNAR profiles and stuffed accounts was not encrypted. In respect of the DNAR profile information, 23andMe stated that the information was posted online in very large CSV (comma-separated values)Footnote 73 files that were difficult to download, view and interpret. However, we note that CSV files are organized in a structured manner such that they can generally be converted into a more accessible format using readily available tools. In the absence of evidence to the contrary, a threat actor with the technical expertise to carry out this wide-scale attack on 23andMe (or another malicious actor who chooses to purchase the data) would likely have the ability to interpret the unencrypted CSV files and extract the personal information contained in the files.
- Furthermore, we note that the raw DNA data downloaded by the Threat Actor, which also was not encrypted, could be interpreted to reveal additional information about an individual, such as an individual’s predispositions in respect of certain diseases and traits (e.g., sex, eye and hair colour). In fact, there is publicly accessible software and technology in existence today that can analyze raw DNA data, with some explicitly advertising compatibility with 23andMe’s datasets.Footnote 74 Therefore, a malicious actor could leverage such software to interpret an individual’s raw DNA data.
- Moreover, given that DNA doesn’t change over time, it will hold information about an individual for their entire lifetime. As science and technology advance, the raw DNA data could allow for more accurate and precise information to be inferred about an individual.Footnote 75 As such, it is possible that malicious actors may be able to use that information in the future in ways that we cannot anticipate now.
Data Has Been and Remains Exposed
- Fourthly, the stolen data has not been recovered. As detailed in paragraphs 3 and 101, the information was advertised for sale in August and October 2023, potentially exposing it to an unknown number of other malicious actors who may have downloaded it for their own purposes. In August 2023, the Threat Actor posted that “14m genomic data have been sold to an Iranian businessman.”Footnote 76
- In light of the above, we believe that there is a high probability of the compromised personal information being misused.
Conclusion on the risk of harm
- Given the high sensitivity of the information compromised and the high probability of misuse, the Privacy Commissioner of Canada and the UK Information Commissioner find that this breach created a risk of harm that met the thresholds under PIPEDA and the UK GDPR respectively, such that 23andMe was required to report the breach to our Offices and to notify affected individuals.
- The Commissioners note that in response to the breach, 23andMe began developing a framework to assess the risk of harm to individuals to ensure that all breaches are treated consistently going forward. In the Preliminary Report, the Commissioners encouraged 23andMe to consider our Offices’ analysis and findings detailed above in developing this framework.
Did 23andMe adequately notify the OPC and ICO about the breach?
- For the reasons explained below, the Privacy Commissioner of Canada and the UK Information Commissioner find that 23andMe’s notifications to the OPC and the ICO were not made in accordance with PIPEDA and the UK GDPR respectively.
- Subsection 10.1(2) of PIPEDA provides that the report to the Commissioner must contain the information prescribed in the regulations and be made in the prescribed form and manner, as soon as feasible after the organization determines that the breach has occurred.
- Section 2 of the PIPEDA Breach Regulations further specifies that a breach notification to the OPC must contain certain information, including:
- a description of the circumstances of the breach;
- the day on which, or period during which, the breach occurred (or approximate period); and
- the personal information that is the subject of the breach, to the extent that the information is known.
- Article 33(3) UK GDPR requires a notification made pursuant to Article 33(1) UK GDPR (notification to the Commissioner) to, at least:
- describe the nature of the personal data breach, including where possible, the categories and approximate number of data subjects concerned and the categories and approximate number of records concerned;
- communicate the name and contact details of the data protection officer or other contact point where more information can be obtained;
- describe the likely consequences of the personal data breach; and
- describe the measures taken or proposed to be taken by the controller to address the personal data breach, including, where appropriate, measures to mitigate its possible adverse effects.
- Article 33(4) UK GDPR states that “where, and in so far as it is not possible to provide the information in a notification at the same time, the information may be provided in phases without undue further delay.”
- Article 33(1) UK GDPR provides, in part, that notification to the ICO must be made without undue delay and where feasible, not later than 72 hours after the organization became aware of it.
Content of 23andMe’s breach notifications to the OPC and ICO
- For the reasons explained below, the Privacy Commissioner of Canada and the UK Information Commissioner each find that 23andMe’s breach notifications to our respective Offices were inadequate as they failed to include complete information about the personal information that was involved or likely to be involved in the breach, and which was known to 23andMe when submitting its breach report.
- 23andMe was alerted of the alleged breach on October 1, 2023, and subsequently verified on October 5, 2023, that the breach was genuine. On October 10, 2023, 23andMe emailed all customers to inform them of the breach and to mandate a password reset. The email explained that certain profile information – which a customer creates and chooses to share via the DNAR feature – was accessed from individual 23andMe accounts.
- On October 13, 2023, the OPC became aware of the breach from several news outlets that reported on the breach. The OPC contacted 23andMe to obtain information about the personal information involved in the breach and the number of Canadians impacted, and to request that 23andMe submit a breach report.
- Following this, in mid-October 2023, 23andMe submitted breach reports to both the ICO and the OPCFootnote 77 and followed up with updated breach reports in late October 2023.Footnote 78 The breach reports explained that the Threat Actor had accessed certain customer accounts, which led to the Threat Actor downloading customers’ DNAR profile information. However, none of these breach reports referred to the possibility that raw DNA data, health reports, and ancestry reports may have been affected in the breach, although – as explained further below – 23andMe knew that such personal information was accessible to the Threat Actor once an account had been accessed.
- At the time of notifying our Offices, 23andMe had already determined that the breach was the result of a credential stuffing attack and that the DNAR profiles for more than a million individuals had been affected. Therefore, while 23andMe may not have known at that time the exact number of accounts that had been stuffed, it would have known that all personal information in a high numberFootnote 79 of stuffed accounts – including ancestry, health reports, and raw DNA data – had been accessible to the Threat Actor. 23andMe was required to inform our Offices that this information had been compromised when it made its initial and supplementary notifications to our Offices in October 2023. 23andMe’s failure to include these details in its notifications is particularly concerning given the high sensitivity of the personal information at issue, and the potential risk of harm to affected individuals, as detailed in the section above.
- The OPC received a further supplementary breach report in December 2023. This report explained that for individuals with stuffed accounts, the Threat Actor had viewed the following: a customer’s settings page; ancestry information; and health reports. In addition, for certain customers, the Threat Actor accessed their self-reported health conditions and uninterpreted genotype data. The OPC noted that several media reports published after the Office’s receipt of this breach report clearly indicated that the breach did not affect DNA data.Footnote 80 Additionally, 23andMe’s December 5, 2023, breach update on its blog did not mention that any raw DNA data had been affected.Footnote 81 As such, the OPC requested further clarification from 23andMe on the matter. In February 2024, 23andMe confirmed that its reference to “uninterpreted genotype data” meant that files including an individual’s complete raw DNA data had been affected.
- The ICO did not receive a supplementary breach report in December 2023 and it was not until June 24, 2024, that 23andMe formally notified the ICO that raw DNA data (and other personal information accessible in a stuffed account) had been affected. 23andMe explained that this was the result of an unintentional omission, which occurred when the individual responsible for notifying the ICO was not included in an email relating to the notification of regulators in December 2023. The UK Information Commissioner finds that there is no evidence to indicate that 23andMe intentionally failed to submit a supplementary breach report to the ICO in December 2023.
Timing of 23andMe’s breach notifications to the ICO and OPC
- In respect of the timing of the breach notification to the ICO, 23andMe’s initial notification to the ICO was submitted on October 15, 2023, 10 days after it confirmed that the breach had occurred, and therefore outside of the 72-hour period specified in Article 33(1) UK GDPR. 23andMe attributed this delay to the fact that it took it until October 12, 2023, to determine what personal data and which customers were affected, and which regulators to notify. Therefore, while the first report of the breach was not submitted within the statutory 72-hour window, 23andMe has provided an explanation for the delay, which the UK Information Commissioner considers to be reasonable in the circumstances.
- PIPEDA does not set a specific timeframe for notifications to be made, and instead requires that the notifications be made “as soon as feasible.” 23andMe first notified the OPC of the breach on October 18, 2023, 13 days after it confirmed the breach to be genuine (and five days after the OPC requested the notification). The OPC acknowledges that organizations may require some time to investigate and confirm the scope of a breach. In this case, the breach affected millions of customers and a large volume of personal information. Therefore, in the circumstances, the OPC accepts that 23andMe provided its breach notification as soon as feasible.
Conclusion on the adequacy of 23andMe’s breach notifications to the OPC and ICO
- In view of the above, as 23andMe failed to notify the OPC and ICO in its October 2023 breach report forms that raw DNA data and other sensitive personal information was accessible in stuffed accounts, the Privacy Commissioner of Canada and the UK Information Commissioner respectively conclude that 23andMe failed to comply with subsection 10.1(2) of PIPEDA and section 2 of the PIPEDA Breach Regulations and the requirements of Article 33(3)(a) and (c) UK GDPR.
Did 23andMe adequately notify affected individuals about the breach?
- For the reasons explained below, the Privacy Commissioner of Canada and the UK Information Commissioner find that 23andMe’s notifications to affected individuals were not, in certain instances, made in accordance with PIPEDA and the UK GDPR, respectively.
- Subsection 10.1(4) of PIPEDA provides that the notification to individuals must contain sufficient information to allow the individual to understand the significance to them of the breach and to take steps, if any are possible, to reduce the risk of harm that could result from it or to mitigate that harm. It must also contain any other prescribed information.
- Section 3 of the PIPEDA Breach Regulations further specifies that a breach notification to affected individuals must contain certain information, including information referred to in section 2 of the PIPEDA Breach Regulations mentioned above.
- Subsection 10.1(6) of PIPEDA provides that the notifications to affected individuals must be made as soon as feasible after the organization determines that the breach has occurred.
- Article 34(1) UK GDPR provides that where a personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the controller must communicate the personal data breach to the affected individuals without undue delay.
- Article 34(2) UK GDPR requires the communication to affected data subjects to describe, in clear and plain language, the nature of the personal data breach and contain at least the information and measures referred to in Article 33(3)(b), (c) and (d) UK GDPR mentioned above.
- 23andMe sent notification emails to affected individuals between October 2023 and January 2024. The content and timing of the notifications to individuals varied based on the type of personal information that was determined to have been impacted.
- Individuals whose DNAR profile information was either posted by the Threat Actor or determined to have been accessed by the Threat Actor were the first to be notified, in October 2023 (“the October Notifications”). Further notifications were sent to certain of these individuals in late December 2023, clarifying that only their family tree information had been affected. Additional notifications were also sent in late December 2023 to individuals who only had their family tree information affected.
- Individuals with stuffed accounts were notified later, in January 2024, almost three months after the breach was first discovered (“the January Notifications”). The content of these notifications varied based on whether the customer’s DNAR profile, Family Tree profile, health information, and/or raw DNA data had been impacted.
- The section below analyzes whether 23andMe adequately notified: (i) individuals whose DNAR profile was impacted and (ii) individuals whose accounts were stuffed.
Notifications to individuals whose DNAR profile was impacted (the October Notifications)
- While the Commissioners accept that the October Notifications were sent promptly, the Privacy Commissioner of Canada and the UK Information Commissioner find that 23andMe failed to include in those notifications all the information that is required pursuant to both PIPEDA and the UK GDPR respectively.
- Despite 23andMe having identified that the personal information of some individuals had been posted for sale online by the Threat Actor, the notifications to those individuals did not include that fact. The Commissioners consider this to be relevant information that could have assisted these individuals to better assess the risk of harm to them and take appropriate steps to mitigate that risk.
Notifications to individuals with stuffed accounts (the January Notifications)
- The Commissioners find that 23andMe did not adequately notify individuals with stuffed accounts, because it did not include all the required information in the notifications. The Privacy Commissioner of Canada also found that these notifications were not made as soon as feasible.
- We understand that some individuals with stuffed accounts also had their DNAR profile impacted, such that these individuals would have received the October Notifications. However, these individuals would not have been notified about their account having been subject to a credential stuffing attack until January 2024. The October 2023 Notifications did not inform them that the highly sensitive personal information contained in their account, such as their health reports and raw DNA data, may also have been accessed by the Threat Actor.
- Moreover, given that the DNAR feature was optional, an individual with a stuffed account who had not activated the DNAR feature would not have had their DNAR information impacted and therefore would not have received a notification in October. These customers would only have been notified that they were impacted by the breach in January 2024, three months after 23andMe confirmed that the breach was genuine.
- 23andMe stated that it did not complete its forensic investigation of the breach until late November 2023, and that it was not until that time that it confirmed that the Threat Actor had accessed and downloaded certain customers’ raw DNA data. That said, 23andMe confirmed at the start of its investigation that a Threat Actor had directly accessed several customer accounts via credential stuffing. Therefore, when 23andMe sent the October Notifications, it had knowledge that information in an undetermined number of customer accounts, such as raw DNA data, was at risk of being compromised. However, 23andMe did not mention this risk to its customers in the October Notifications.
- The UK Information Commissioner has concluded that, by failing to mention this risk in the October Notifications to individuals, 23andMe failed to adhere to the requirements of Articles 34(1) and (2) UK GDPR regarding the content of 23andMe’s notifications to affected individuals. Article 34(2) UK GDPR requires that communications to affected individuals should at least include the information referred to in points (b), (c) and (d) of Article 33(3) UK GDPR, including a description of the likely consequences of the breach.
- In light of this, the notifications sent to affected UK-based individuals should have included that there was the possibility of unauthorised access to raw DNA data.
- Subsection 10.1(4) of PIPEDA provides that the notification shall contain sufficient information to allow the individual to understand the significance to them of the breach. In the absence of evidence to the contrary, the fact that it was possible that an affected individual’s raw DNA data may have been compromised was relevant to those individuals’ understanding of the risk to them resulting from that breach. The Privacy Commissioner of Canada therefore finds that 23andMe contravened subsection 10.1(4) of PIPEDA by not including this information in its October Notifications.
- In any event, while 23andMe determined in late November 2023 which accounts had been stuffed, it only began notifying these individuals on January 3, 2024, more than a month later. 23andMe did not provide an acceptable explanation for this delay, which is particularly concerning given the highly sensitive personal information that is accessible within a customer’s account. Therefore, the Privacy Commissioner of Canada also finds that 23andMe did not issue notifications to individuals with stuffed accounts as soon as feasible.
- Finally, we note that the January Notifications did not include the following information:
- the fact that the account (setting) information was accessed during the breach. While 23andMe did include this information in some of the January Notifications, it did not do so for all of the notifications. We understand that this information could have included the individual’s full name, date of birth, sex at birth, gender, email address, country and postal code of current residence, and weight and height; and
- the period during which the breach occurred. 23andMe only stated the date when the Threat Actor posted samples of stolen data online. In January 2024, 23andMe had completed its forensic investigation and knew that the breach had occurred from April 2023 to September 2023. 23andMe should have included this information in its January Notifications.
Conclusion on the adequacy of notifications sent to affected individuals
- OPC: In light of the above, the Privacy Commissioner of Canada concludes that 23andMe failed to comply with the requirements of:
- subsection 10.1(4) of PIPEDA and section 3 of the PIPEDA Breach Regulations by failing to include the following information:
- in the October Notifications, the fact that the Threat Actor had posted information online for individuals whose DNAR profiles had been impacted;
- in the October Notifications, the possibility that affected users’ raw DNA data had been impacted;
- in the January Notifications, the period during which the breach had occurred, which was known by 23andMe; and
- in the January Notifications, the account information that was subject to the breach.
- subsection 10.1(6) of PIPEDA by failing to notify, as soon as feasible, all individuals whose accounts had been stuffed.
- subsection 10.1(4) of PIPEDA and section 3 of the PIPEDA Breach Regulations by failing to include the following information:
- ICO: In light of the above, the UK Information Commissioner concludes that 23andMe failed to adhere to the requirements of Articles 34(1) and (2) UK GDPR regarding the content of 23andMe’s notifications to affected individuals.
Was 23andMe’s methodology adequate to identify and notify individuals whose raw DNA was downloaded by the Threat Actor?
- In addition to the inadequacies noted above regarding the January Notifications to individuals whose accounts had been stuffed, our Offices had concerns as to whether 23andMe had notified all affected individuals whose raw DNA data may have been subject to the breach. In the Preliminary Report, we identified multiple issues with 23andMe’s original methodology used during the post-breach forensic investigation, leading us to believe that 23andMe may have failed to correctly identify all raw DNA downloads carried out by the Threat Actor.
- We note that the content of the January Notifications varied depending on whether 23andMe had determined that the Threat Actor had downloaded the individual’s raw DNA data. Where 23andMe had determined, according to its forensic methodology detailed below, that the raw DNA data download was attributable to the Threat Actor, it notified the individual that the Threat Actor had “downloaded or accessed their uninterpreted genotype data”.
- 23andMe hired a third party to conduct a forensic investigation into the breach, with the support of 23andMe staff. As noted in paragraph 17 above, 23andMe claimed solicitor-client privilege over certain reports and communications related to the forensic investigation and refused to disclose these records to our Offices. Our analysis of the forensic process is based on 23andMe’s answers to our inquiries and our own analysis of the data 23andMe provided.
23andMe’s original methodology to identify raw DNA downloads by the Threat Actor
- At the time of the breach, to download raw DNA data, a customer had to first make a download request via their 23andMe account. After this request, there was a delay while the data was prepared. Once prepared, the data was placed into a third-party cloud storage area, and the customer was then informed by email that their data was available to download. The customer was then required to log in to their 23andMe account and click on a link to begin the download process.
- When a customer clicked the link to begin the download, the event was logged by the third-party cloud service provider. However, during the period of the breach, 23andMe did not collect and retain the original third-party logs. Instead, 23andMe created and stored its own custom logs of such download events, using some information from the original third-party logs.
- Due to a misconfiguration in these custom logs, an invalid IP address was associated with the download activity. 23andMe was therefore unable to use the custom log to identify suspicious downloads conducted by IP addresses associated with the Threat Actor. Instead, to determine whether a raw DNA download was likely attributable to the Threat Actor, 23andMe had to correlate information from other event logs. More specifically, 23andMe searched for logins from an IP address that it had attributed to the Threat Actor and then examined whether a raw DNA download event was recorded for the same account within the six hours that followed the login.
Identification of potential raw DNA downloads by the Threat Actor
- In the Preliminary Report, the Commissioners shared their concern that 23andMe’s original methodology to identify suspicious downloads appeared to be flawed and that 23andMe should have employed a broader methodology to identify raw DNA downloads that may have been initiated by the Threat Actor. In the absence of any means of definitively identifying raw DNA downloads by the threat actor, the Commissioners proposed that a broader methodology may have been more appropriate. More specifically, 23andMe could have considered any raw DNA data that was downloaded from a stuffed account between the time that the account was compromised and October 9, 2023 (i.e., the global password reset) to have been initiated by the Threat Actor.
- Our Offices’ analysis of the logs provided by 23andMe indicated that such an approach would have identified over 270 accounts with raw DNA downloads potentially initiated by the Threat Actor, as opposed to the 18 identified and notified by the company. According to 23andMe, 10 of these 270 accounts belonged to individuals in Canada and 8 to individuals in the United Kingdom.Footnote 82 The Commissioners therefore recommended that 23andMe reanalyse the log data to confirm the number of individuals whose DNA was likely downloaded by the Threat Actor and notify any of those whom it had not previously identified.
- In response to the Preliminary Report, 23andMe re-examined all raw DNA downloads from compromised accounts throughout the breach period. 23andMe’s updated approach examined many more data points than its original methodology, including approximate locations and historic internet service providers, to make a more informed assessment of each download event to determine if it was suspicious. According to 23andMe’s new analysis, the Threat Actor downloaded the raw DNA of a total of four individuals worldwide (this did not include any individuals in Canada or the United Kingdom). The Commissioners have not independently verified the updated figures provided by 23andMe.
Conclusion on Issue 2
- In light of the above, the Commissioners find that the breach created a risk of harm to affected individuals that met the risk of harm thresholds under both PIPEDA and the UK GDPR, such that 23andMe was required to notify our Offices and affected individuals of the breach. The Commissioners find that 23andMe’s notifications to our Offices and affected individuals were not made in accordance with PIPEDA and the UK GDPR respectively.
Assessment of 23andMe’s current compliance with its breach notification requirements
- Given the contraventions identified above, in their preliminary report the Commissioners issued detailed recommendations to 23andMe to ensure compliance with subsection 10.1(4) of PIPEDA, subsection 3(c) of the PIPEDA Breach Regulations and Article 34(2) UK GDPR (read with Article 33(3)(c) UK GDPR), which are summarized below :
- review of its logs integration process, to ensure that its logging system for customer activity within the platform is free from errors and misconfigurations;
- update its policies and procedures to ensure proper breach notifications to regulators and affected individuals; and
- implement proper procedures and policies to ensure that all personal data breaches, including 23andMe’s assessment of the risk of harm resulting from a breach, are recorded and documented appropriately and are made available to regulators where required.
- In response to the Preliminary Report, 23andMe informed our Offices how it had:
- reconfigured it logs so that its security team can better track and identify malicious activities; and
- updated relevant processes, including, its Risk Management Framework, Cyber Incident Response Procedure and its Privacy and Security Incident Response Policy, among others.
- In light of 23andMe’s response, the Commissioners find that 23andMe addressed the issues identified in the Preliminary Report. As such, the Commissioners find the Breach Notification aspects of this matter to be resolved.
Conclusion
- In light of the above, the Privacy Commissioner of Canada and the UK Information Commissioner have reached the following conclusions:
Conclusions of the Privacy Commissioner of Canada
- Issue 1: 23andMe contravened Principle 4.7 of Schedule 1 of PIPEDA by failing to implement appropriate safeguards to ensure the protection of the highly sensitive personal information of its customers. In light of the additional and enhanced safeguard measures implemented by 23andMe during the course of this investigation, the Privacy Commissioner of Canada finds this issue to be well-founded and resolved.
- Issue 2: 23andMe contravened section 10.1 of PIPEDA and sections 2 and 3 of the PIPEDA Breach Regulations, given the inadequacies in its breach notifications to the OPC and to affected individuals identified above. In light of the measures implemented by 23andMe to address the contraventions identified, the Privacy Commissioner of Canada finds this issue to be well-founded and resolved.
Conclusions of the UK Information Commissioner
- Issue 1: 23andMe infringed Articles 5(1)(f) and 32(1) UK GDPR by failing to implement appropriate technical and organisational measures to ensure the integrity and confidentiality of its processing systems and services and its customers’ personal information; and
- Issue 2: 23andMe failed to adhere to the requirements of Articles 33(3)(a) and (c), UK GDPR regarding the content of 23andMe’s notifications to the ICO in a manner which aggravated the infringements set out in respect of Issue 1 above. In addition, the UK Information Commissioner finds that 23andMe failed to adhere to the requirements of Article 34(1) and (2) UK GDPR (read with Article 33(c) UK GDPR), regarding the content of its notification to affected customers, but the UK Information Commissioner has not treated this as an aggravating factor.
Other: Future of 23andMe
- On March 23, 2025, following the breach and in the face of mounting financial losses, 23andMe Holding Co. and certain of its subsidiaries, including 23andMe, filed for Chapter 11 bankruptcy under the US Bankruptcy Code in the United States Bankruptcy Court for the Eastern District of Missouri.
- While the Commissioners find that 23andMe has implemented measures to address the concerns we identified in the Preliminary Report, we understand that 23andMe’s bankruptcy may result in the sale or transfer of the company and/or customers’ sensitive personal information, including DNA and health information, to a another company.
- During the course of the investigation, our Offices wrote to the US Trustee overseeing 23andMe’s bankruptcy proceedings to emphasise the legal requirement for personal information relating to individuals located in the United Kingdom and Canada to be handled in compliance with respective data protection laws.Footnote 83
- A Consumer Privacy Ombudsman has been appointed to conduct an examination of any transaction involving the sale of 23andMe and/or its assets and its impact on customers’ personal information. A sale approval hearing is scheduled to take place on June 17, 2025, in the US Bankruptcy Court for the Eastern District of Missouri.Footnote 84
- If any company successfully acquires the personal information of 23andMe’s customers, our Offices will provide that company with a copy of this Report to ensure it is aware of its obligations under PIPEDA and the UK GDPR, including to protect sensitive information with robust security safeguards. Our Offices will not hesitate to take appropriate action if we consider there to be evidence of non-compliance with the applicable data privacy laws in our respective jurisdictions.
- Date modified:

